Sponsored by Splunk
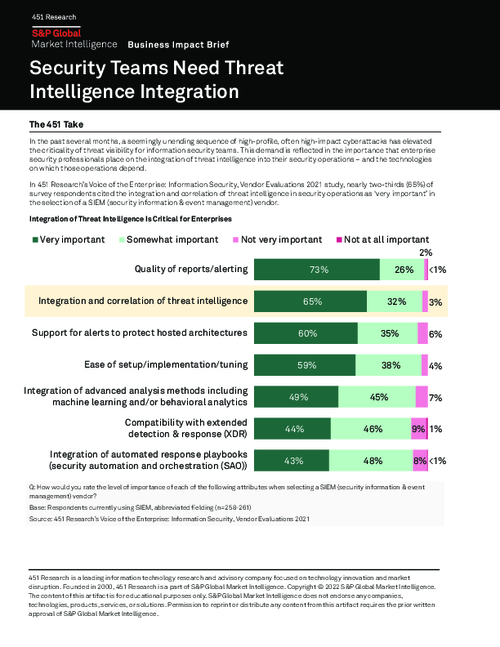
451 Research: Security Teams Need Threat Intelligence Integration
Sponsored by Palo Alto
BLOCKED! Five Strategies for Ironclad Endpoint Security
Sponsored by Cyolo
Secure Digital Transformation Requires Identity-Based Access Control
Sponsored by Mandiant
Determine your Cyber Security Risk with Repurposed Ransomware
Sponsored by Mandiant
Why Security-Conscious Organizations Use Compromise Assessments
Sponsored by Mandiant
Combating Ransomware
Sponsored by Deepwatch
How to Manage Growing Threats, Tighter Budgets (eBook)
Sponsored by Mandiant
The Defender’s Advantage Cyber Snapshot Issue 2
Sponsored by Mandiant
Mandiant Advantage Threat Intelligence Free
Sponsored by Mandiant
The Defender's Advantage Cyber Snapshot
Sponsored by Mandiant
APT42's Crooked Charms, Cons and Compromises
Sponsored by Mandiant
Remediation and Hardening Strategies for M365 to Defend Against APT29
Sponsored by CybelAngel