Sponsored by hCaptcha
Sponsored by Pure Storage
Ransomware: Before, During and After the Attack
Sponsored by Sophos
Cyberattacker Behaviors and Tactics Used for Incident Response During 2021
Sponsored by Sophos
Checklist: How to stop Ransomware In Its Tracks
Sponsored by Sophos
Block Ransomware: The Best Practices in IT Security
Sponsored by Sophos
Is your Endpoint Security the Right One?
Sponsored by Proofpoint
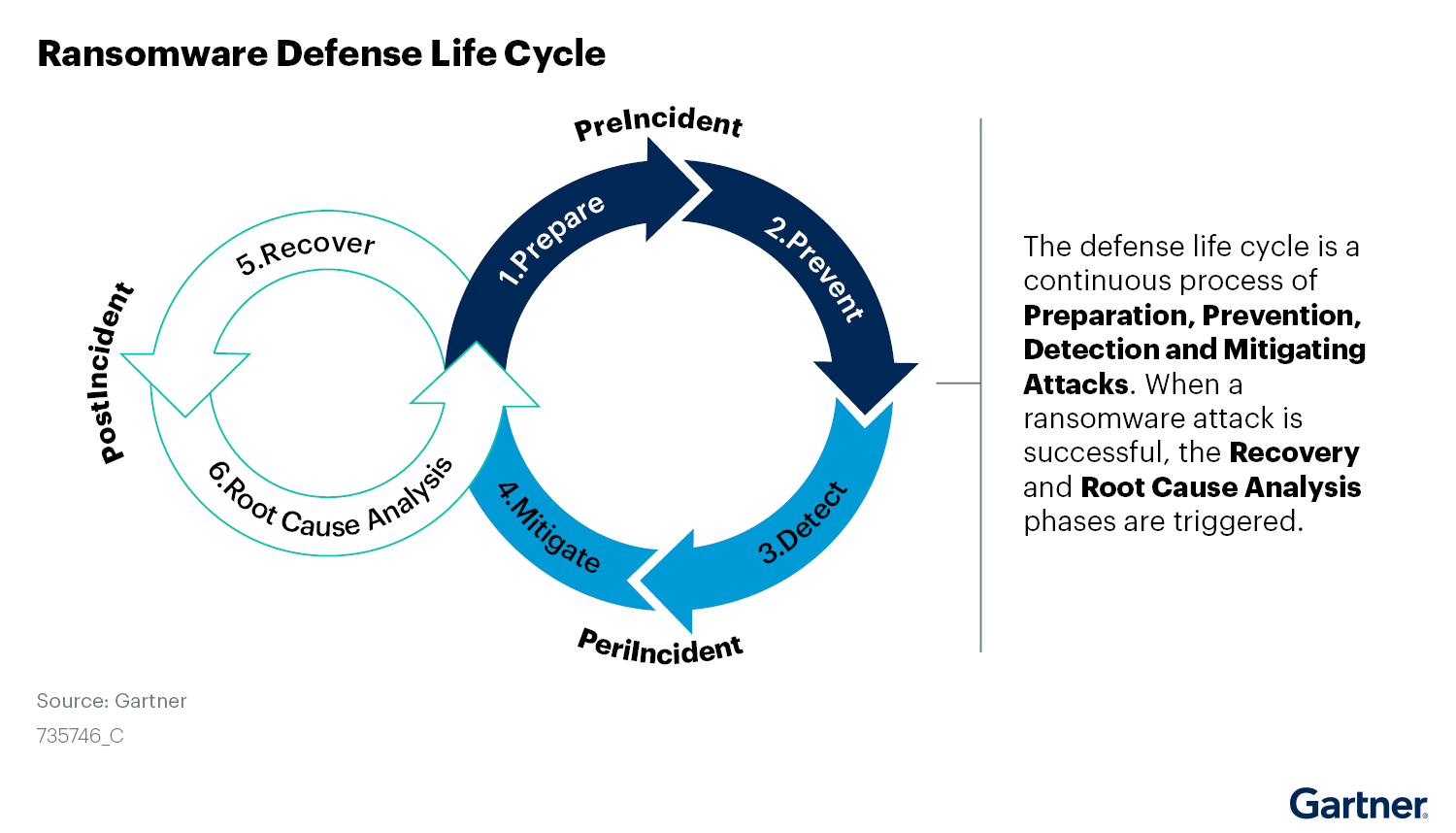
Gartner® Report How to Prepare for Ransomware Attacks
Sponsored by Optiv
Why Improved Recovery From Cyber Incidents Is Critical
Sponsored by Expel
Expel Quarterly Threat Report - Q2 2022
Sponsored by CyberArk
Endpoint Security Review: A Defense-in-Depth Perspective on Ransomware
Sponsored by Gigamon
2022 Survey Results | Ransomware, Cryptojacking and Beyond: Emerging Security Trends
Sponsored by SecureLink
Is Your Organization Safe Against Ransomware?
Sponsored by Veritas
Best Practices to Combat the Threat of Ransomware
Sponsored by Tanium
A New Class of Converged Endpoint Platforms for a Better Breed of IT SecOps
Sponsored by Mimecast