Sponsored by Micro Focus
Sponsored by Micro Focus
Process or Speed? Why You Need Both to Make DevOps Work
Sponsored by VASCO
Securing Mobile Banking Apps
Sponsored by VMware
Eight Common Pitfalls of App and Desktop Virtulization
Sponsored by VMware
Digital Workspace Basics
Sponsored by VMware
Enterprise Mobility Trends to Watch
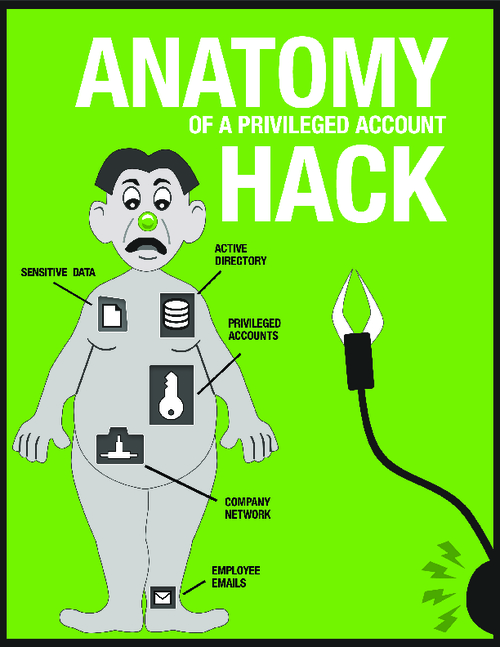
Sponsored by Thycotic
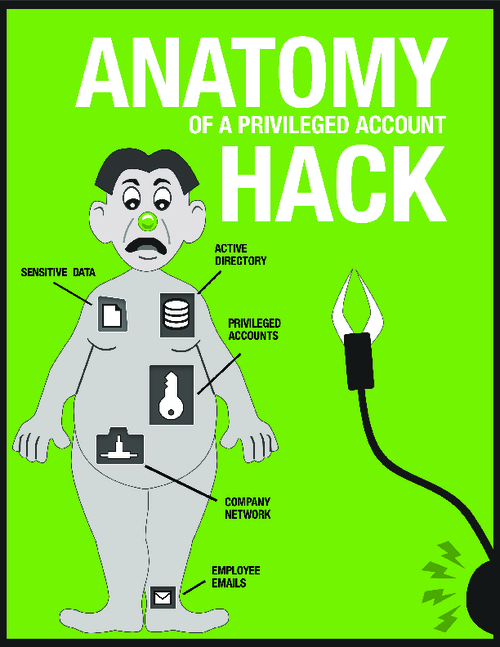
The Anatomy of a Privileged Account Hack
Sponsored by Thycotic
Why Are Hackers so Successful at Targeting Privileged Accounts?
Sponsored by Digital Guardian
A Practical Approach to GDPR Compliance
Sponsored by Digital Guardian
GDPR Compliance Requires Data Loss Prevention
Sponsored by CrowdStrike
Evaluating EDR Vendor Claims: Not All Endpoint Protection is Equal
Sponsored by Venafi
Dark Web Research: Criminals Pay Top Dollar for Your Certificates
Sponsored by BitSight
Making Risk Management More Effective with Security Ratings
Sponsored by BitSight
5 Ways Your Vendor Risk Management Leaves You In The Dark
Sponsored by BitSight