Endpoint Security , Fraud Management & Cybercrime , Governance & Risk Management
Updated Agent Tesla Malware Disables Endpoint Protection
Sophos: Information-Stealing RAT Found in Many Malicious Email Attachments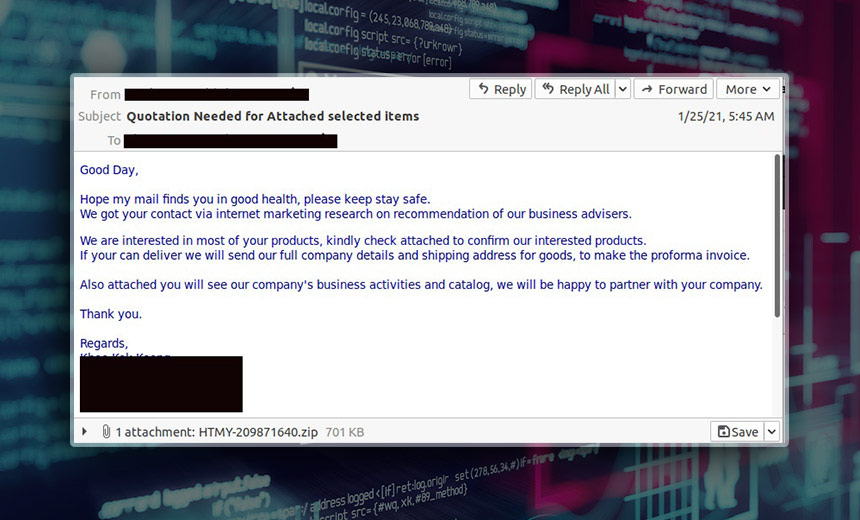
The operators behind the Agent Tesla remote access Trojan have updated the malware to enable it to disable endpoint protection software and have added features to hide communications, according to a report from the security firm Sophos released Tuesday.
See Also: Enabling Government for Modernized IT
Two versions of the Agent Tesla information stealer are operating in the wild, and both use the new evasion techniques, according to the report. Operators of the updated malware now can use encrypted Telegram channels or Tor-based clients to communicate with command-and-control servers, the report notes.
The Agent Tesla malware, which has been circulating since 2014, has been updated regularly, the researchers say.
"It has been among the top malware families distributed via email in 2020,” says Sean Gallagher, a senior security researcher at Sophos. “In December 2020, Agent Tesla payloads accounted for around 20% of malicious email attachment attacks intercepted by Sophos scanners. A variety of attackers use the malware to steal user credentials and other information from targets through screenshots, keyboard logging and clipboard capture."
Sophos says that its recent Agent Tesla detections have been in the U.S. and Europe, but the variants have been used globally (see: Beware: Agent Tesla Infostealer Now More Powerful).
Version 2 and 3
Version 2 and version 3, spotted in June 2020 and the fall of 2020, respectively, share several traits, including a set of global variables that determines the functionality and behavior of the malware, Sophos says. The malware operator provides the values for these variables in the form of a configuration file that governs a wide variety of actions, the report notes.
One major update in version 3 is the ability to make sandboxing and static analysis more difficult and to evade endpoint security. This is accomplished by going beyond the use of packers to obfuscate code, with multistage malware installers pulling in components hosted in plain view on legitimate websites, such as Pastebin and Hastebin, the Sophos researchers note.
The new versions of the Agent Tesla installer also attempt to overwrite code in Microsoft's Anti-Malware Software Interface, or AMSI, according to the report.
Overwriting the code makes "all the AMSI scans of memory appear to be invalid,” the report states. “This sabotages endpoint protection software dependent on AMSI, by essentially making them skip further AMSI scans for dynamically loaded assemblies within the AgentTesla process.”
Other evasive actions in versions 2 and 3 include options to install and use the Tor anonymizing network client, and the Telegram messaging API, for command-and-control communications. Gallagher says.
Additional Persistence
Both updated versions of AgentTesla have improved ability to maintain persistence on the infected system, the report says.
"The persistence option just ensures that the malware executes if the computer is rebooted,” Gallagher notes. “Without it, Agent Tesla executes just once and sends back one set of credentials. But the persistent version would attempt to scrape credentials every time the computer is rebooted.”
In version 3 of the malware, the variable that enables persistence also triggers the collection of the infected system's external IP address - one data point the malware uses to fingerprint its host for identification by its operator. The malware does this by using the public web API of ipify.org, researchers say.
Other than the IP address, the fingerprinting data of the malware's version 3 collects processor name, total memory, operating system, user name, computer name, current date and time, the report notes.
The stolen credentials are then bundled by Agent Tesla with the host fingerprint data and transmitted back to the command-and-control server once during execution. "The malware doesn't repeat this process unless it has been configured for persistence and the infected system restarts," the Sophos researchers note.
"The credential-stealing function also includes code which launches a separate thread to exfiltrate browser cookies,” Gallagher says. “While this code is present in all the samples of AgentTesla from both version 2 and version 3, it isn't always used. Also, this feature is not set from the configuration file - so, perhaps, it's a premium feature attackers must buy from Agent Tesla's developer."
Another feature of in both versions of the malware is screenshot exfiltration. If this option is enabled, a timer is initialized that captures an image of the infected system's screen through .NET libraries and sends the image to the command-and-control as JPEG images over the configured network protocol, the report notes.