The Threat-Centric Security Approach
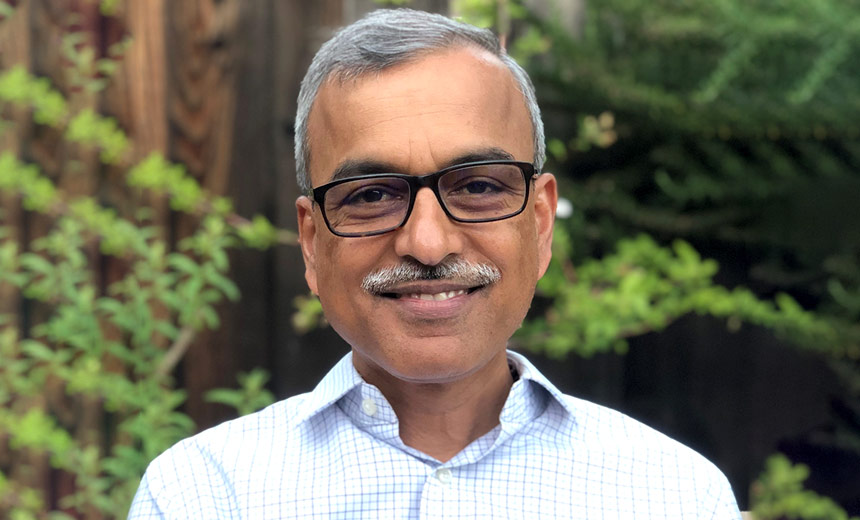
Oliver Friedrichs, SVP Cloud Technology, Sourcefire
Advanced threats require an advanced security strategy. Oliver Friedrichs of Sourcefire recommends a threat-centric security approach. In this interview, he explains exactly what that entails.
See Also: Assessing Threats Outside the Perimeter
Despite the layers of security that organizations have deployed, they are still falling victim to infections and intrusions. The problem is the fundamental approach to security, Friedrichs says.
In this video interview, Friedrichs explains:
- The definition of a threat-centric approach;
- How it differs from the traditional methods;
- Technology solutions that will enable the approach.
Friedrichs is Senior Vice President, Cloud Technology Group at Sourcefire, providing direction for the company's cloud-based technology strategy and executing Sourcefire's product development roadmap for the cloud platform. He brings more than 15 years of expertise in developing innovative security technologies and has worked closely with numerous government and commercial organizations to help address their cybersecurity requirements. Friedrichs joined Sourcefire in January 2011 as part of the Immunet acquisition where he was founder and CEO.
Additional Summit Insight:
Hear from more industry influencers, earn CPE credits, and network with leaders of technology at our global events. Learn more at our Fraud & Breach Prevention Events site.