RBS WorldPay Sentence Too Light?
Fraudster Gets 30 Months for Role in $9 Million Heist
A federal judge in Atlanta this week handed down the first U.S. sentence in the RBS WorldPay heist. The November 2008 incident was one of the first globally coordinated attacks the payments industry had ever seen.
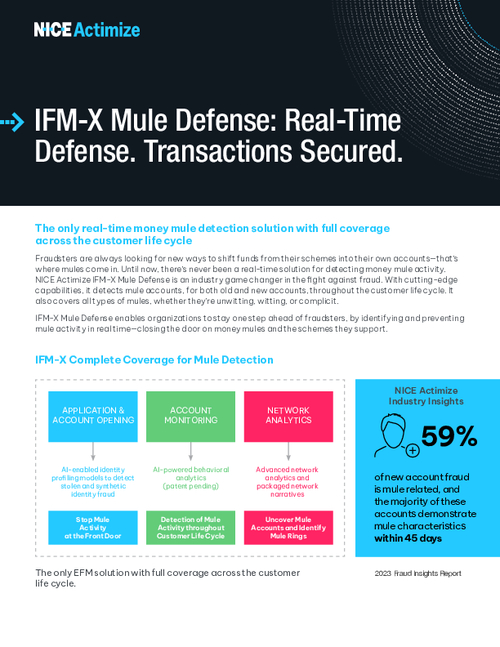
See Also: Delving Deeper: 2023 Fraud Insights Second Edition
Sonya Martin, a 45-year-old Chicago resident who was the accused leader of one of the hacking cells involved in the massive heist, who pleaded guilty to conspiracy to commit wire fraud, was sentenced to serve 30 months in federal prison. She also was ordered to pay $89,000 in restitution, and she'll have five years of supervised release.
In a statement about the sentencing, Sally Quillian Yates, the U.S. Attorney for Northern Georgia, says the case and the investigation set an international example.
"This case demonstrates the growing expertise and reach of law enforcement in combating international cybercriminals," she says. "We will continue to work with our law enforcement partners throughout the world to investigate and prosecute those who defraud victims in the United States, wherever the perpetrators may be."
But Julie McNelley, a fraud analyst at Aite, a financial services consulting firm, says that while it's always good to see cybercriminals put behind bars, the sentencing in this case is too light to send a strong message.
"There are many more individuals to fill the shoes of Sonya and serve as runners to monetize the fraud," McNelley says. "However, to the extent that law enforcement agencies can get better at collaborating to bring people involved with cybercrime to justice, it will send a message that there is risk involved in engaging in these acts."
Martin's Role in the Scheme
Martin, whose primary residence is in Nigeria, was arrested in March 2011 at John F. Kennedy International Airport in New York as she was attempting to travel to London.
The scheme Martin helped to coordinate against Atlanta-based retail payments processor RBS WorldPay (now known as WorldPay U.S. Inc.), and its customers was extremely well-organized and sophisticated. With counterfeit cards created from debit details that cyberthieves accessed when they hacked WorldPay's payments processing network, Martin and others fraudulently withdrew funds from more than 2,100 ATMs all over the world, including the United States, Russia, Ukraine, Estonia, Italy, Hong Kong, Japan and Canada.
Over the course of a 12-hour period, criminals in 280 cities worldwide drained more than $9 million from U.S. bank accounts and put more than 1.5 million U.S. cardholders at risk.
The Heist
Authorities say once the hackers gained access to the RBS WorldPay network, they used sophisticated techniques to decrypt customer data that the processor maintained about payroll debit cards. Employees can use these types of cards to make purchases and withdraw cash from ATMs, and that made these accounts attractive to the cyberthieves.
The hackers also were able to raise the balances and ATM withdrawal limits on 44 compromised payroll accounts. They then provided runners or "cashers," like Martin, with associated debit card numbers and PINs, allowing them to withdraw funds at ATMs.
Martin supervised a cashing crew in Chicago, according to court records. She also manufactured counterfeit debit cards with the stolen payroll card numbers and PINs and gave the counterfeit cards to underlings she recruited and supervised. Together, her team fraudulently withdrew approximately $80,000 from various Chicago ATMs during the early morning hours of Nov. 8, 2008.
Throughout the global cash-out, the hackers monitored the fraudulent ATM withdrawals in real-time from within the computer systems of RBS WorldPay. Once the withdrawals were completed, the hackers destroyed data stored on the card-processing network to conceal their illegal activity. RBS WorldPay, however, discovered the unauthorized activity and immediately reported the breach to authorities.
Others Charged
Though not all the players connected to the heist have been brought to justice, authorities in the U.S. and other nations have worked collaboratively since 2009 to indict, arrest and sentence a handful. In addition to Martin, 10 others have been indicted. Five of those 10 have been arrested; among those five, two have been sentenced and two await trial.
In November 2009, federal authorities in Atlanta indicted eight eastern European members of the ring. Four of the eight - Sergei Tsurikov, 25, of Tallinn, Estonia; Viktor Pleshchuk, 28, of St. Petersburg, Russia; Oleg Covelin, 28, of Chisinau, Moldova; and one known only as "Hacker 3" - were charged with conspiracy to commit wire fraud, wire fraud, conspiracy to commit computer fraud, computer fraud, access device fraud and aggravated identity theft.
The other four - Igor Grudijev, 31, Ronald Tsoi, 31, Evelin Tsoi, 20, and Mihhail Jevgenov, 33, all of Tallinn, Estonia - were indicted for access device fraud.
In March 2010, Russian authorities arrested three of those indicted suspects - Pleshchuk, Tsurikov and Covelin. Russian law prohibits extradition of its citizens. But U.S. authorities were able to have Tsurikov extradited, since he had been arrested by Estonian authorities a year earlier. Tsurikov was arraigned in August 2010. He is still awaiting trial.
In September 2010, Pleshchuk was tried in Russia and received a six-year suspended sentence with four years of probation. He received no jail time.
Whether Covelin, whom authorities allege discovered the flaw in RBS WorldPay's system that allowed hackers to break the encryption used to protect card data, was tried in Russia is not known.
Federal authorities have not issued any additional information about the five others indicted.
In August 2010, Vladislav Anatolievich Horohorin, 27, a.k.a. "BadB" of Moscow, was arrested in France and in June 2012 was extradited to the U.S. and arraigned for his role in the scheme. He was ordered detained, pending his trial.
Horohorin had been indicted in 2009 for device fraud and aggravated identity theft in connection with the case. He is thought to be one of the most prolific sellers of stolen payment card data.
And in February 2011, a Russian court handed down a five-year suspended sentence with no jail time to Yevgeny Anikin, 27, for the role he played. The lighter sentence was reportedly given because of the assistance Anikin offered authorities during the investigation.