Phishing-as-a-Service Platform Offers Cut-Rate Prices
Customers of 'Robin Banks' Platform Have Netted $500,000
A rising cybercrime syndicate has decided it's easier to sell phishing kits than teach other cybercriminals to hook victims themselves, charging as little as $50 a month for a simple campaign.
Although the prices quadruple for more sophisticated campaigns and online support, prices offered by phishing-as-a-service vendor "Robin Banks" are a considerable step down from other comparable providers who charge between $150 to $300 a month, says network security company IronNet.
The company spotted a large-scale email and SMS campaign earlier this summer using the Robin Banks platform with the goal of accessing credentials and financial information pertaining to Citibank and Microsoft logon account credentials.
Researchers first saw Robin Banks in March 2022 and say they assess that its customers have netted more than $500,000 from victims by using the platform tools. Intended victims reside in the United States, United Kingdom, Canada and Australia.
Platform Details
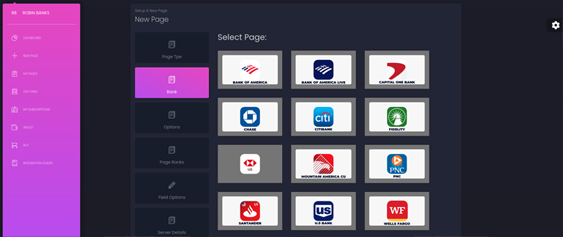
The PhaaS provider sells phishing kits to cybercriminals specializing in social engineering scams, offering a "quick and easy" way for threat actors of all skill levels to perform network intrusions.
The kits include prepackaged folders that contain all the code, graphics and configuration files needed to create phishing pages. They also include features such as curated databases of targets or branded email templates that are designed for easy deployment and can be reused.
Users can select from a large library of brands to impersonate, including well-known U.S. banks such as Wells Fargo and Bank of America, as well as brands such as Netflix in Canada and T-Mobile.
"The primary motivation for scammers using this kit appears to be financial," IronNet researchers say. Advanced threat actors could also use the services to "gain initial access to corporate networks for ransomware or other post-intrusion activities," they say.
Researchers found that the interested buyers could access the robinbanks.in website by creating an account login with email and password. The payment was to be made using Bitcoin.
"The Robin Banks website has a more sophisticated yet user-friendly webGUI than 16Shop and BulletProftLink - two well-known phishing kits that are also notably more expensive than Robin Banks," the researchers say.
Robin Banks gained several new customers in a few months and is among a handful of PhaaS platforms that consistently update their templates, IronNet says.
How the Kits Work
Attackers send a malicious link via SMS or email. The victim, on clicking the link, is presented with a phishing page content. In case a system detects a potential bot, a separate page comes into action that helps with the completion of a reCAPTCHA. This process stops web scanners from detecting phishing pages. Once this process is completed, the victim is redirected to the main landing page containing phishing content hosted centrally at the Robin Banks infrastructure.
Once a victim starts entering in data, the domain uses the POST method to transmit data to the Robin Banks application programing interface, where criminal clientele can view it on their platform portal account.
The domain transmits two tokens - one used by the client to interact with the Robin Banks platform and the other identifying the victim. The number of POST transmissions depends on how many webpages victims are asked to fill out - each time a victim encounters another page requesting information, such as for payment card data, the domain sends a separate data transmission to the API.
The system architecture is possibly a fail-safe "in case the victim decides to quit the form prior to finishing it," IronNet writes.