Critical Infrastructure Security , Governance & Risk Management , Operational Technology (OT)
New Survey Shows 6 Ways to Secure OT Systems
Survey Conducted by Rockwell Automation and ISMG Warns of OT Vulnerabilities
A year ago, a ransomware attack against Colonial Pipeline shut down gasoline supplies to the U.S. East Coast for nearly a week, in what became the largest-ever attack against oil and gas systems. Today, federal authorities are warning of spillover attacks against critical infrastructure from the Russia-Ukraine cyberwar.
See Also: An All-in-One Vulnerability Management, Detection, and Response Solution
Critical infrastructure specialists have warned about these scenarios for years, and there's good reason for hand-wringing. The critical infrastructure sector is plagued with numerous vulnerabilities, new and existing cybersecurity gaps, and an expanding attack surface.
Organizations with operational technology and industrial control systems should start preparing now, or this perfect storm of threats could result in the "big shutdown" - a large-scale disaster with broad, harmful implications, according to a 2022 survey conducted by Rockwell Automation and ISMG, Cybersecurity Preparedness in Critical Infrastructure: Avoiding 'The Big Shutdown.'
"Seventy-three percent of the surveyed critical infrastructure organizations said they experienced cybersecurity breaches," says Nicole Darden Ford, vice president of global security and CISO at Rockwell Automation. "What a large number. It tells us that we should be paying very close attention to our preparedness so that we can effectively mitigate threats before they ever become breaches."
The survey included 122 responses from senior industrial security leaders, with roles ranging from CISO and head of security to plant engineers and business managers. Responses covered 20 organizations that rely on OT security, including oil and gas, energy, chemical, water/wastewater and manufacturing companies. (see: Proof of Concept: Key Steps for Improving OT Security).
"A large number of breaches are preventable. About 80% of breaches use entry points that are already known. It can be solved with tools and processes that already exist. Let's take patching, for example. Research shows that 66% don't have an effective patching strategy in place. Like we saw with the coronavirus, the longer a virus - or an exploit, in this case - is out there, the more it evolves."
– Nicole Darden Ford, Rockwell Automation
The survey report points to six basic ways organizations can tighten OT and ICT security: through an improved asset inventory program; a zero trust strategy that addresses data, assets, applications and services; reliable identity and access management controls; a secure architecture that separates IT and OT systems; effective patch management; and improved recovery and restoration planning.
"A large number of breaches are preventable," Darden Ford says. "About 80% of breaches use entry points that are already known. It can be solved with tools and processes that already exist. Let's take patching, for example. Research shows that 66% don't have an effective patching strategy in place. Like we saw with the coronavirus, the longer a virus - or an exploit, in this case - is out there, the more it evolves."
The survey shows these organizations are taking steps to improve cybersecurity preparedness and resiliency. It also finds that many are struggling to overcome hurdles such as budget and talent shortages, lack of management prioritization and lack of insight about how to best shore up defenses. Among the key findings were:
Automate Asset Inventory Processes
Security organizations can only protect the assets they know about, which is why asset inventory management is key to OT security. In most cases, inventories are being updated quarterly at best, which could leave operations vulnerable to attack. Nearly one-third - 30% - of those surveyed in manufacturing and machinery, healthcare, public health, emergency services, pharmaceuticals and chemicals said they conduct asset audits less than once a quarter.
Automated asset inventories help prevent attacks that result from lack of visibility. A variety of automated tools and services are available to simplify the inventory assessment process both for IT and OT.
While frequency may vary by industry, Ford recommends organizations conduct asset inventories at least monthly. "In fact, many of our clients are moving to real-time asset inventory," she says. "We can automate this process, so it's generally less painful for organizations. This is what we recommend.
Adopt a Zero Trust Strategy for Data, Assets, Applications and Services
Threat actors target business-critical systems to disrupt operations and in the case of ransomware, pressure organizations to pay the ransom. But the survey finds only 56% of organizations had identified and prioritized business-critical systems. These systems include ICS and production line applications and data that could be locked up by ransomware. Other critical systems that should be prioritized include production operations, data security or integrity, communications, supply chain continuity and customer services.
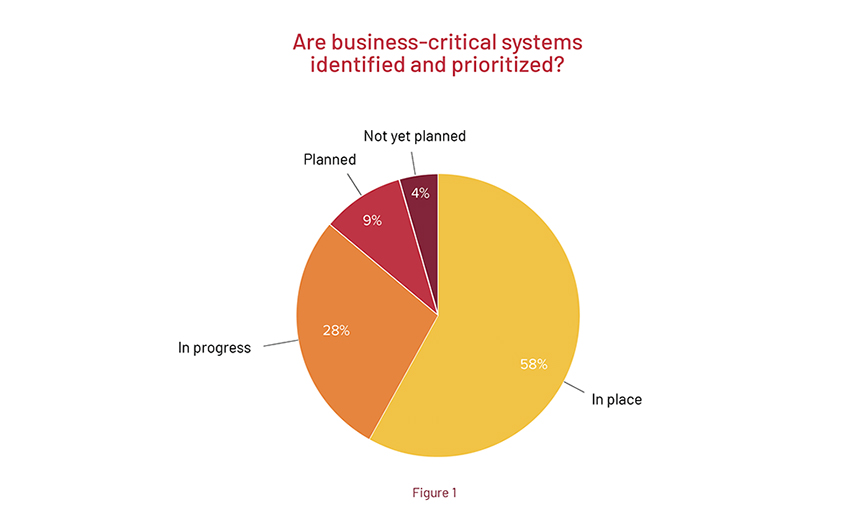
While cybersecurity software protects the perimeter, the traditional trust model relying on firewalls and VPN access is allowing attackers to move laterally throughout the enterprise. Zero trust strategy focuses on protecting data, assets, applications and services, prioritizing each based on their criticality. These protect surfaces need the right cybersecurity controls in place and applied in priority order.
Ensure Reliable Identity and Access Management Controls
The move to remote working during the novel coronavirus pandemic and new policies for hybrid working have turned remote access into a prime target for attackers. One of the cornerstones of zero trust is a reliable identity and access management system that monitors who is requesting access, to which applications and data, from where, using what device, at what time - with controls that track behavioral norms. While 69% of survey respondents report having secure remote access in place, that statistic may be misleading. Some remote access systems use outdated security, often relying on passwords alone to allow access to critical systems.
Identity and access management systems must ensure proper monitoring, enforce access policies and controls, and integrate multifactor authentication to lower the threat of compromised passwords.
Build a Secure Architecture That Separates IT and OT Systems
A fundamental principle of OT security is the need to create an air gap between ICS and OT systems and IT systems. This basic network cybersecurity design employs an industrial demilitarized zone to prevent threat actors from moving laterally across systems, but the survey finds that only about half of organizations have an IDMZ within their OT architecture, and 8% are working on it. The healthcare, public health and emergency services sectors were especially behind. Nearly 40% of respondents in those sectors don't have plans to implement an IDMZ.
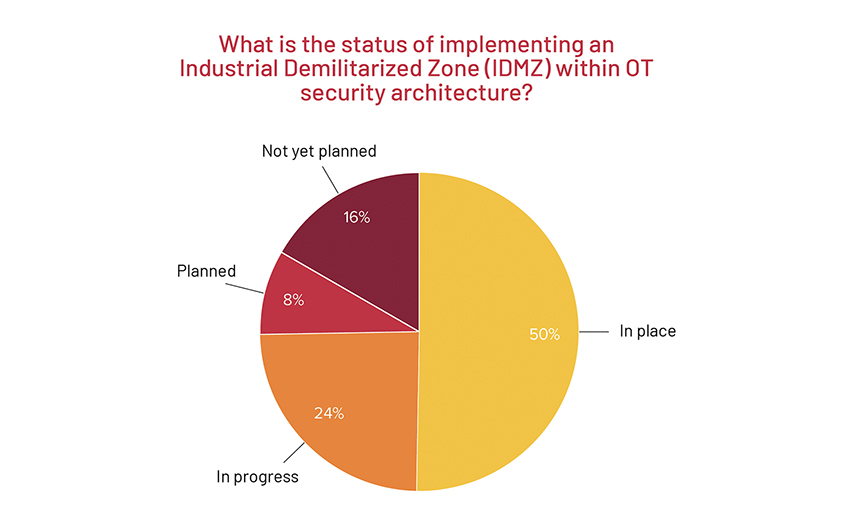
Implementing a DMZ is a basic best practice, Ford says. "The risk is lateral movement where breach can move from IT to OT or vice versa, or from low-value network assets to high-value network assets," Ford says. "The more attackers can penetrate your infrastructure, the greater damage and downtime they can cause. Segmentation in DMZ, demilitarized zones, provide an air gap between IT and OT, and additional segmentation can further protect business-critical assets with strong access controls, firewalls and policy rules based on zero trust."
Ensure Efficient and Effective OT Patch Management
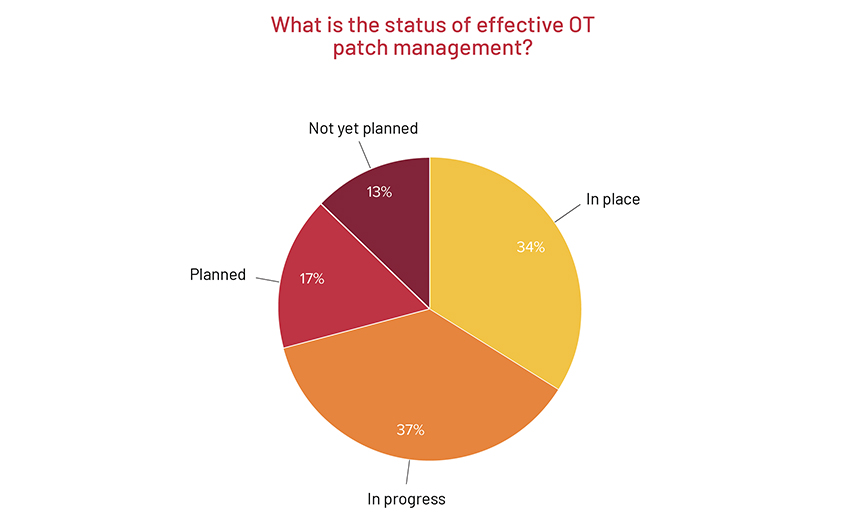
OT patching is a significant area of vulnerability. According to the survey, patch management is either not considered an important practice, not funded or simply too complicated to undertake. Only 34% of respondents reported implementing an effective OT patch management program, and 12% still haven't planned a patching approach. In the manufacturing and machinery vertical, 42% of surveyed organizations don't have effective patch management program in place or even in progress.
Just over half of organizations cited effective security procedures for removable media, which can be used to inject malware or steal data. Similarly, only 49% of organizations have implemented segmentation or microsegmentation to protect business-critical systems. Efficient and effective OT patch management starts with deep industrial experience and OT cybersecurity expertise, which can help to avoid common pitfalls and implement best practices for patching.
"We don't want cyberattackers to have easy access and time to get better at exploiting those gaps," she says. "We need to stop them before they can inflict greater damage."
Improve Recovery and Restoration Planning
With nearly three-fourths of critical infrastructure providers experiencing breaches, the need for fast and effective recovery is paramount to business operations.
"It goes way beyond downtime, damage or ransom. It now includes risk of litigation, high cyber insurance costs, reputational harm, supply chain problems, public safety and so many other issues."
– Nicole Darden Ford, Rockwell Automation
A ransomware attack in 2021 forced JBS, the world's largest meat processing company, to stop cattle-slaughtering operations at 13 of its meat processing plants. Even though the company paid an $11 million ransom to cybercriminals, the disruption resulted in meat shortages in grocery stores nationwide. Colonial Pipeline paid $5 million in ransom but it took six days for the company to recover, costing millions of dollars in lost revenues plus untold economic impacts from the ensuing gas shortage.
Less than half of those surveyed - 46% - said they are ready with recovery processes today and have systems, data and operational procedures in place to restore operations quickly after a cyberattack.
Recovery and restoration planning should be as common an operational practice as asset maintenance, which is central to reliable operational uptime, Ford says.
"Many costs of breaches go unreported and it goes way beyond downtime, damage or ransom," Ford says. "It now includes risk of litigation, high cyber insurance costs, reputational harm, supply chain problems, public safety and so many other issues."
Taking the Next Step Toward OT Security
Ford advises organizations to ensure they have the right tools in place, skilled resources who can manage both IT and OT security, and a plan for improving existing systems and assets. The first step, she says, is conducting a risk assessment that identifies vulnerabilities and helps prioritize time and investments.
"I'm encouraged that many responses in our research report stated that several measures were in progress or planned, so attention and action are taking shape," Ford says. "In my opinion, we cannot move fast enough."
Read the survey report