DDoS Protection , Fraud Management & Cybercrime , Fraud Risk Management
Millions of Devices Potentially Vulnerable to DNS Flaws
Report: Healthcare and Government Organizations Particularly at Risk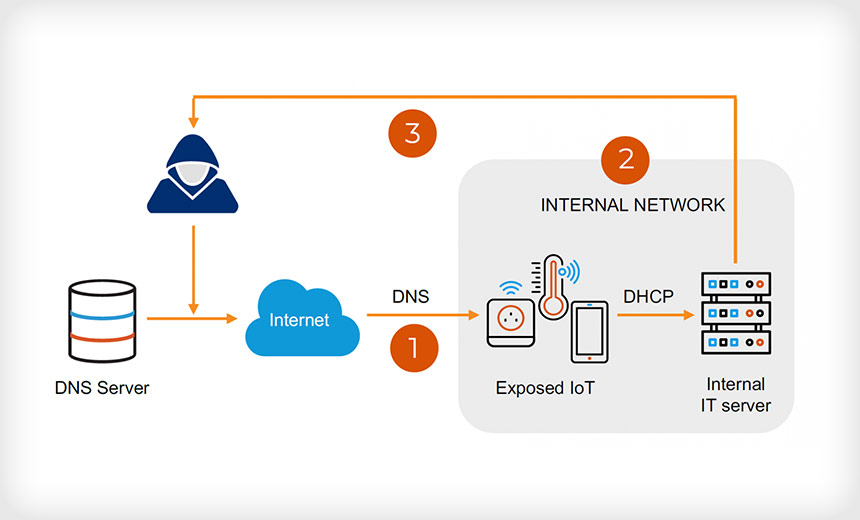
Forescout Research Labs and the Israeli security firm JSOF have found nine Domain Name System vulnerabilities affecting four TCP/IP stacks that, if exploited, could lead to remote code execution or denial-of-service attacks - potentially on millions of devices.
See Also: Risk Management Framework: Assessing and Monitoring NIST 800-53 Controls for DoD
The group of vulnerabilities, dubbed Name:Wreck, affects the FreeBSD, IPNet, NetX and Nucleus NET stacks. The widespread use of these stacks, together with external exposure of the vulnerable DNS clients, could dramatically increase the attack surface for organizations, JSOF says.
"Organizations in the healthcare and government sectors are in the top three most affected for all three stacks," Forescout says. "If we conservatively assume that 1% of the more than 10 billion deployments … are vulnerable, we can estimate that at least 100 million devices [could potentially be] impacted by Name:Wreck."
Forescout notes that TCP/IP stack vulnerabilities are particularly dangerous because stacks implement basic network communication for all IP-connected devices, including IoT, OT and IT. Forescout says none of the Name:Wreck vulnerabilities are being exploited in the wild, but attacks could result in data theft or DoS extortion incidents.
"The vulnerabilities we are presenting now affect DNS clients, which is a somewhat overlooked part of DNS security that also allows for severe attacks," Forescout says. "Not only are TCP/IP stacks widespread, they also are notoriously vulnerable due to codebases created decades ago and an attractive attack surface, including protocols that cross-network perimeters and lots of unauthenticated functionality."
Exploiting the vulnerabilities is not a simple task. An attacker must find a way to send a malicious packet in reply to a legitimate DNS request. So the attacker would have to run a man-in-the-middle attack or be able to use an existing vulnerability, such as DNSpooq, between the target device and the DNS server to pull this off, Malwarebytes says in its note on Name:Wreck.
The Vulnerabilities
Six of the vulnerabilities affect the Nucleus NET stack and one each affects FreeBSD, IPNet and NetX. Forescout says only IPNet has not issued an updated version that patches these vulnerabilities. The security firm recommends organizations patch their systems as soon as possible.
Discovery and Mitigation
Because some IoT devices cannot be patched, Forescout is making available an open-source script that uses active fingerprinting to detect devices running the affected stacks so that the security issue can be addressed or the device taken out of service. Forescout says it will regularly update the script with new signatures.
Forescout also recommends that organizations enforce segmentation controls and proper network hygiene, implement patches upon release and monitor all network traffic for malicious packets.
The security company also recommends configuring devices to rely on internal DNS servers as much as possible and then closely monitoring external DNS traffic because exploitation requires a malicious DNS server to reply with malicious packets.
The U.S. National Security Agency and the Cybersecurity and Infrastructure Security Agency recently released new guidance on how to choose and deploy a Protective Domain Name System service to strengthen security. PDNS services use a resolver that helps to prevent connections to known or suspected malicious sites (see: Tips on Selecting a Protective DNS Service.)