Data Masking & Information Archiving , Fraud Management & Cybercrime , Next-Generation Technologies & Secure Development
IBM Shipped Malware-Infected Flash Drives to Customers
Security Alert Says Drives Contain Trojan Tied to Cybercriminals
In a security alert, IBM is warning that it inadvertently shipped malware-infected USB flash drives to some of its storage hardware customers as well as to customers of some Lenovo-branded products.
See Also: Government Agencies: 10 Reasons to Get on the Container Storage Bandwagon
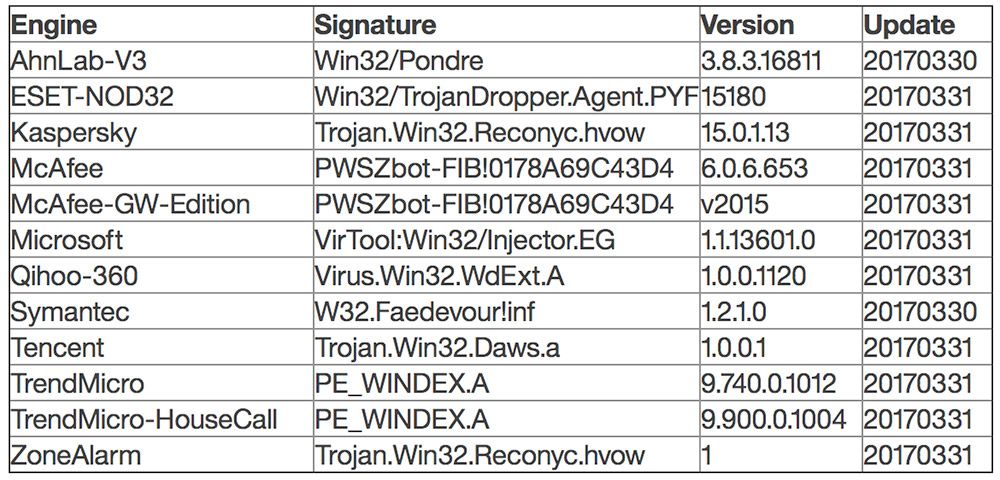
A Trojan - known as Faedevour, Pondre and Reconyc - is present on USB flash drives that have been distributed to some users of IBM and Lenovo Storwize systems, which are virtualizing RAID computer data storage systems.
"IBM has detected that some USB flash drives containing the initialization tool shipped with the IBM Storwize V3500, V3700 and V5000 Gen 1 systems contain a file that has been infected with malicious code," IBM says in its alert.

The infected USB flash drives have the part number "01AC585" on them, IBM notes.
The malware does not infect Storwize systems, IBM's security alert says, and USB flash drives issued for encryption key management do not contain the malware. It also says that while inserting the infected drive into a Windows, Mac or Linux system will result in the malware being placed onto that system, it does not automatically execute.
"IBM has taken steps to prevent any additional USB flash drives being shipped with this issue," the company says in its alert.
An IBM spokeswoman declined to comment about how the malware found its way onto the flash drives, how many customers have received those drives or what steps the company is taking to prevent a recurrence.
But the security alert says that the malware should have been flagged by anti-virus software. "If you have used the initialization USB flash drive from one of the [designated] IBM products ... and have inserted it into a desktop or laptop to initialize a Storwize system, IBM recommends you verify your anti-virus software has already removed the infected file or alternatively remove the directory containing the identified malicious file in the manner described below," it says. "IBM recommends ensuring your anti-virus products are updated, configured to scan temporary directories, and issues identified by the antivirus product are addressed."
Flash Drives Shipped with Storwize Boxes
IBM says that malware-infected USB flash drives have shipped with the following products:
- IBM Storwize V3500 - 2071 models 02A and 10A
- IBM Storwize V3700 - 2072 models 12C, 24C and 2DC
- IBM Storwize V5000 - 2077 models 12C and 24C
- IBM Storwize V5000 - 2078 models 12C and 24C
These products are also branded as "IBM Storwize for Lenovo," and a similar security alert was issued by Lenovo. Infected flash drives shipped with:
- IBM Storwize for Lenovo V3500 - 6096 models 02A and 10A
- IBM Storwize for Lenovo V3700 - 6099 models 12C, 24C and 2DC
- IBM Storwize for Lenovo V5000 - 6194 models 12C and 24C
No infected flash drives were shipped for IBM or Lenovo Storwize Systems that have serial numbers that begin with the characters 78D2, IBM reports.
Malware: Reconyc
Anyone who has received an infected USB flash drive and used it to install Storwize tools onto a system, IBM says, will find that the malware is present in the following temporary folders:
- On Windows systems: %TMP%initTool
- On Linux and Mac systems: /tmp/initTool
According to security firm Kaspersky Lab, the malware in question - which it refers to as the Trojan.Win32.Reconyc family - is designed to download additional attack code onto infected endpoints and has been in circulation since at least 2014.
"Malicious programs in this family are used by cybercriminals to install additional software on the infected computer," according to a Reconyc analysis published by Kaspersky Lab. "The malicious program copies its executable file to a temporary folder on the user's computer and modifies the operating system registry, enabling the malware to run automatically after the user logs in to the system. The malware decrypts itself, performs extraction from its resources section and launches other malicious programs."
Destroy or Wipe the Drives
IBM recommends that anyone in possession of an infected flash drive securely destroy it. Secure flash drive destruction techniques include using Windows or Mac operating system utilities to overwrite all data on the device - preferably twice. Devices also can be rendered useless, for example, with a screwdriver and hammer.
IBM also offers directions for repairing the USB flash drive so it can be reused, which involves deleting the contents of the device, downloading a FixCentral initialization tool from IBM and then installing it on the drive instead.