Endpoint Security , Governance & Risk Management , Internet of Things Security
Here's How Your Phone Charger Could Be Hacked
Tencent Researchers Modify Charger Firmware to Deliver Too Much Power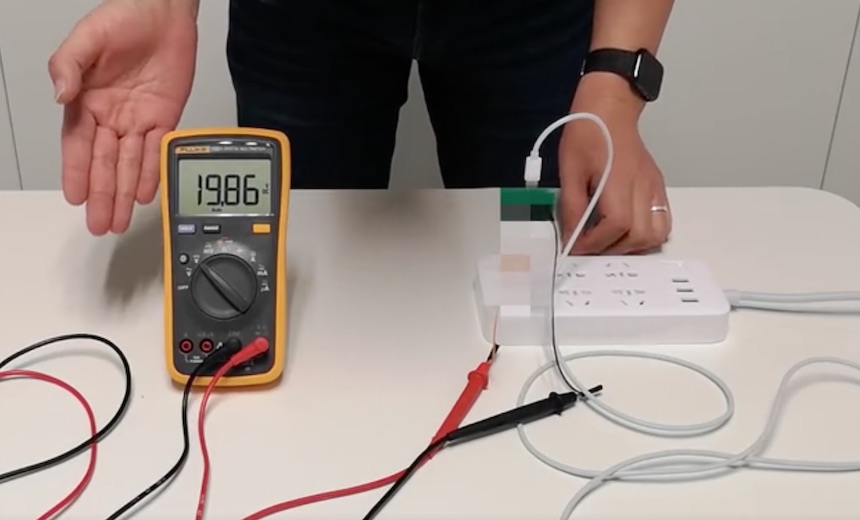
Fast charging has been a boon to the device-dependent world. The protocols that enable fast charging deliver more voltage to compatible devices, reducing the time it takes to recharge.
See Also: Case Study: Global Pharma Expands OT Visibility and Strengthens Security
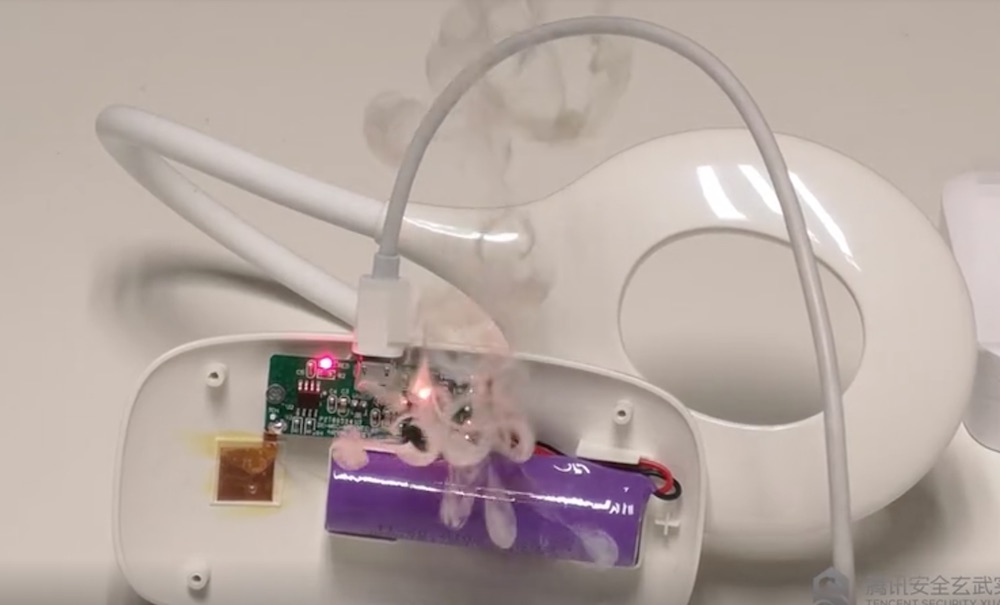
But there’s a new risk highlighted by researchers at China's Tencent’s Security Xuanwu Lab. By tampering with the firmware in some chargers – an attack they call BadPower – the voltage delivered can be increased, exceeding the limit for a phone or other device. The result - smoke, a broken device and potentially a fire.
“In most cases, the power overload will cause the related chips in a powered device to break down and burn, resulting in irreversible physical damage,” according to a translation of Xuanwu Lab blog post. “In rare cases, BadPower attacks may also affect the physical environment around the device.”
Flash and Puff of Smoke
Some chargers can deliver as many as 20V, whereas 5V has typically been standard. Chargers developed for fast charging run firmware that’s designed to match what a device can handle and prevent the transmission of too much power.
Xuanwu Lab researchers write that the firmware in some chargers can suffer from memory corruption problems or fail to perform proper security checks before software is written to the charger.
“Attackers can use these problems to rewrite the firmware of the fast-charging device to control the power supply behavior of the device,” it writes.
To compromise a charger, the researchers created a hardware device that looks like a mobile phone. When it’s connected to a charger, however, it actually delivers malicious firmware. A malicious charger can report to a device that it will deliver 5V when it’s actually delivering 20V.
A demonstration video, which is at the end of the blog post, shows how a charger can be infected and then the result when it’s connected to a device: a flash and a puff of smoke.
Guard Your Chargers
The lab says it found at least 234 fast-charging devices on the market and tested 35. Of those, 18 made by eight brands were vulnerable to BadPower attacks. The researchers didn't identify the vulnerable models or brands.
The lab also looked at the chips which enabled fast charging. Xuanwu Lab says it surveyed 34 fast-charging chip makers and found that 18 produce chips that could be updated to fix the problems.
That’s encouraging because the researchers write that most BadPower issues can be fixed by updating the firmware. Also, some devices aren’t necessarily vulnerable to BadPower even if the chargers are due to built-in electrical overload protections.
Manufacturers can help fix the BadPower attacks, Xuanwu Lab says. They should either verify that firmware updates coming over USB are legitimate or not allow updates via that avenue.
Also, the firmware should be checked for common software vulnerabilities. Chip fuses could also be incorporated into non-fast charging devices to prevent modified chargers from delivering too much current.
“It is recommended that powered devices that support fast charging continue to check the input voltage and current after power negotiation to confirm that they meet the negotiated range,” the researchers write.
And on the user side: keep your chargers close at hand, just as you would with your computer, the researchers advise.