Fraud Management & Cybercrime , Fraud Risk Management , Malware as-a-Service
Do Ransomware Operators Have a Russian Government Nexus?
Supposed Rivals Said Maze Gang Had Moscow Backing - But Was That Just Sour Grapes?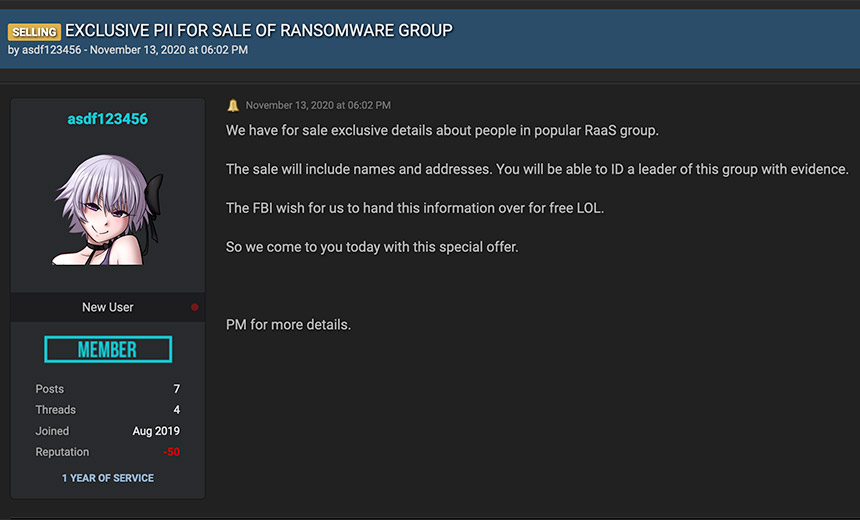
Maze was one of the most notorious and successful ransomware operations of recent years until its "retirement" last November. The group pioneered the data-leaking model that involves first stealing victims' data, then using the threat of leaking it to try to force victims to pay.
See Also: The State of Organizations' Security Posture as of Q1 2018
The strategy worked, helping fuel a boom in ransomware profits and leading numerous other operations to follow suit.

One rumor that emerged before Maze's exit, however, was that it had the backing, if not direct support, of the Russian government, and that the group was merely another name for the notorious cybercrime gang called Evil Corp.
Some chatter suggested Maze - and its apparent successor, Egregor - might have had a connection with the Russian government's principal security agency, the FSB, although the nature of that connection remains unclear.
As the security researcher known as @pancak3lullz states, a self-proclaimed member of the Sodinokibi, aka REvil, ransomware-as-a-service operation gang alleged that two members of the eight-person Maze gang were Maxim Yakubets and Konstantin Kozlovsky, and that Yakubets was working for the Russian government.
Yakubets, aka "aqua," has been on the FBI's most-wanted list for some time. The bureau accuses the Ukraine-born Russian national of having launched Zeus Trojan attacks beginning a decade ago, as well as committing bank fraud. "Yakubets is also allegedly the leader of the Bugat/Cridex/Dridex malware conspiracy" - aka Evil Corp - "wherein he oversaw and managed the development, maintenance, distribution, and infection of the malware," it says.
#REvil has claimed to have information that exposes the actors behind #Maze/#Egregor and that they are directly connected with the Russian government - that #EvilCorp, #Maze, etc. are all one group operated by 8 people involved with the FSB. pic.twitter.com/Y7votbk1pP
— pancak3 (@pancak3lullz) November 30, 2020
But the attempt to tie an alleged cybercrime kingpin to the Maze operation, as cybersecurity journalist Catalin Cimpanu has reported, may simply have been sour grapes on the part of REvil and other rivals.
Or it may have been a scam promulgated by a third party trying to make a quick buck. In a Nov. 13, 2020, post to the "leaks market" on cybercrime forum RaidForums that appears to be part of the attempts to advance these claims, a new user with the handle "asdf123456" wrote: "We have for sale exclusive details about people in popular RaaS group. The sale will include names and addresses. You will be able to ID a leader of this group with evidence. The FBI wish for us to hand this information over for free LOL. So we come to you today with this special offer."
In response, a "god user" on the site posted: "He was spotted and banned on XSS forum," referring to a Russian-language cybercrime forum. "Most likely he is trying to rip off some stupid researchers and cops."
Twitter user @Bank_Security posted a response to the RaidForums post, allegedly from a REvil representative, which simply read: "It's fake."
Comment by REvil representative: pic.twitter.com/Eh9ZuWTbFf
— Bank Security (@Bank_Security) December 1, 2020
Moscow Connection?
In recent interviews, some security experts have pointed to some of the above posts as potential proof that Russia may be running or supporting ransomware gangs, beyond authorities' typical "we'll look the other way so long as you do us the occasional favor" cybercrime code that appears to still be in effect in that nation.
But others question whether the supposed evidence that's surfaced to date can be used to bolster any such suggestions.
"I’m not aware of any real evidence which points to that connection actually existing - except, that is, the assertions of somebody who claimed to be a member of the REvil group, and those assertions carry near-zero weight," says Brett Callow, a threat analyst at Emsisoft.
On the other hand, such a connection "is certainly not beyond the realm of possibility," he says, since so many nation-state attackers and cybercrime operators blur together.
"For example, OFAC sanctioned Evil Corp, stating its leader 'provides direct assistance to the Russian government’s malicious cyber efforts, highlighting the Russian government’s enlistment of cybercriminals for its own malicious purposes,'" Callow notes, referring to the U.S. Treasury Department’s Office of Foreign Assets Control sanctions.
Sometimes that’s because government employees moonlight as criminals in their free time, and other times it can be because governments try to hide their endeavors behind the facade of a criminal enterprise.
More examples: "WastedLocker has been attributed to Evil Corp, and there is also believed to be a connection between Evil Corp and BitPaymer, and DoppelPaymer is a fork of BitPaymer," Callow says. "Additionally, groups have affiliates and contract specialists, both of which may also work for other groups - or possibly even for governments. All of this means the line between state and nonstate actors can be very blurry."
Maze Exits, Egregor Debuts
In the meantime, Maze appears to have exited the scene - or did it?
If so, then it leaves behind a legacy of innovation, including having pioneered back in November 2019 the trend of stealing and then leaking data to force victims to pay. More than 20 other ransomware operators followed suit. As the gang saw increasing success, experts say it began recruiting specialists with more sophisticated hacking, cloud environment and other skills to help it take down larger, more lucrative targets. And last August, call center operators apparently tapped by Maze began cold-calling victims to try to pressure them into paying.
Unlike some other ransomware operations, Maze both ran its own attacks as well as used the ransomware-as-a-service model, in which affiliates receive crypto-locking malware from operators. For every victim that an affiliate infected who pays a ransom, the affiliate and operator shared in the profits. Threat intelligence firm Intel 471 says Maze found that using affiliates was a much easier and more reliable way to maximize profits than simply running all attacks using its in-house crew.
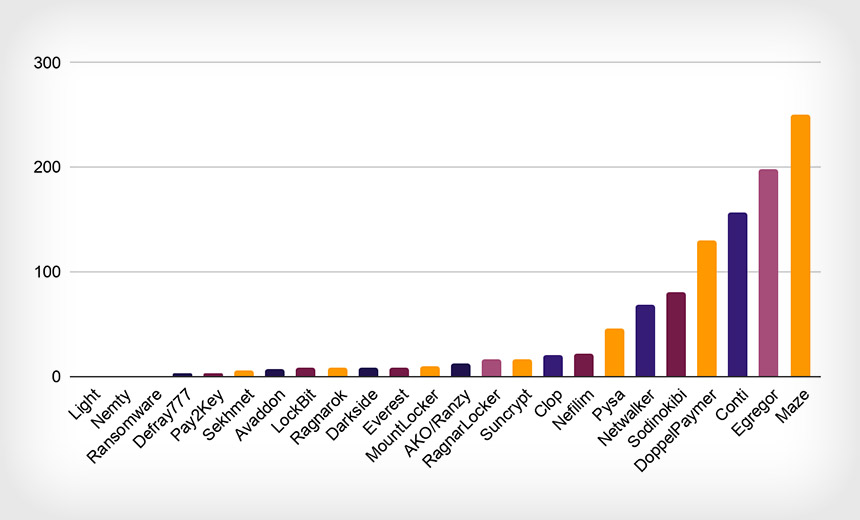
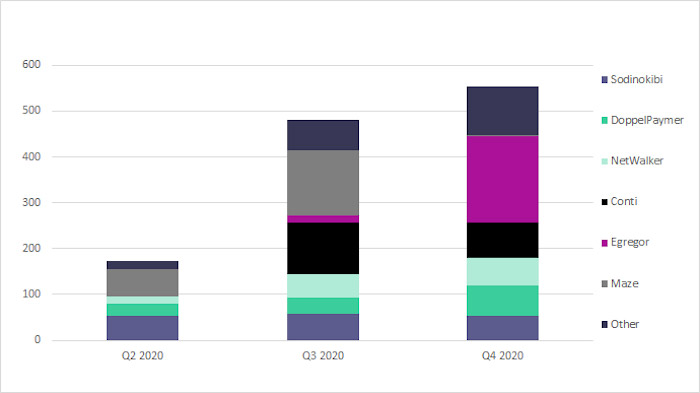
Now, Egregor appears to have seized Maze's mantle. "As you saw Maze kind of go back in the shadows and begin to phase themselves out, Egregor really stepped up and they are posting a new compromise just about every day on their public website," says Greg Foss, a senior cybersecurity strategist at VMware.
The Egregor ransomware-as-a-service operation made a splashy debut last October, when it hit U.S. bookstore chain Barnes & Noble, followed by video game developers Ubisoft and Crytek and big-box retailer Kmart. Last year, "Egregor victims increased 240% from Sept. 25 to October, and another 43% from October to Nov. 17," Digital Shadows reports.
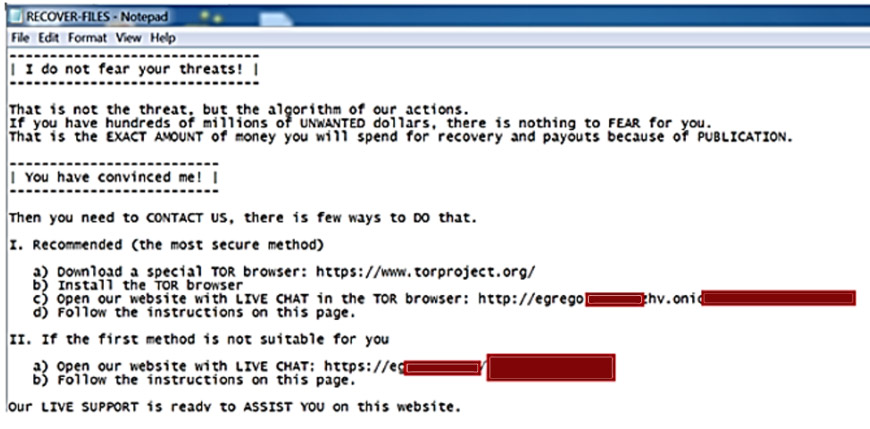
Circumstantial evidence for a connection between Maze and Egregor includes Egregor's malware sharing technical similarities with Maze, as cybersecurity firm Recorded Future has noted, as well as both having similar data-leaking sites and near-identical ransom notes, as Bleeping Computer has reported.
The FBI last month warned that Egregor had been tied to known attacks against at least 150 corporate networks around the world. Individual ransom demands have sometimes reached $4 million.
"The group initially racked up victims at an unprecedented rate," Emsisoft's Callow said in a recent interview. "This is probably because multiple threat actors joined Egregor's affiliate program after the Maze group ended its operation, taking with them details of compromised networks that had yet to be exploited."