Card Not Present Fraud , Cybercrime , Fraud Management & Cybercrime
Card-Skimming Malware Campaign Hits Dozens of Sites Daily
Lock Down Magento E-Commerce Software or See Card Details Get Routed to Moscow
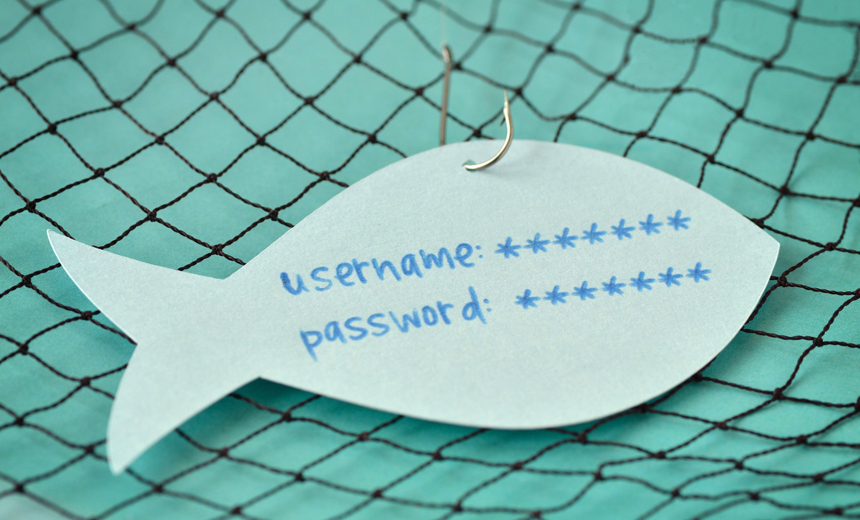
More than 7,000 e-commerce sites in the past six months have been infected with harmful JavaScript designed to harvest customers' payment card details as they finalize their orders.
See Also: The Power of Identity in Financial Services
So warns Willem de Groot, a security consultant and researcher based in the Netherlands, who says that online card-skimming software that communicates with a domain hosted in Moscow, magentocore[dot]net, is being used to infect 50 to 60 e-commerce sites a day.
"The victim list contains multimillion-dollar, publicly traded companies, which suggests the malware operators make a handsome profit," de Groot writes in a blog post, noting that the malicious code is designed to work with legitimate Magento e-commerce software. "But the real victims are eventually the customers who have their card and identity stolen."
Magento, which Adobe Systems announced plans to acquire in May, is one of the most widely used e-commerce platforms. So it's perhaps no surprise that the software has naturally become a favored target of payment card thieves, who have seized upon users' sometimes insecure configurations or used brute-force attacks to gain access to deployed software.
The payment card industry is still battling to stop criminals from swiping card details and replaying the details in fraudulent schemes. One way to use the details is in so-called card-not-present transactions online. Australia, for example, has seen card-not-present fraud rise 14 percent in a one-year period (see Australia Battles Fraudulent Online Purchases).
While cybercriminals' primary aim so often appears to be to steal payment card data, shoppers' personal data would also be up for grabs. That has implications for compliance with the General Data Protection Regulation, Europe's strict data protection regime, writes Peeter Marvet of Zone.ee, an Estonia hosting provider, in a blog post (see Under GDPR, Data Breach Reports in UK Have Quadrupled).
Replace Malware With ... Malware
Whoever is behind the magentocore campaigns has been having a productive run, de Groot says.
Based on his internet scans, de Groot has found 7,339 online stores have been hacked in the last six months. And since 2015, de Groot has counted at least 20,000 websites that have at been infected by the malicious JavaScript at least once.
Websites don't necessarily catch on quickly after an infection. "The average recovery time is a few weeks, but at least 1,450 stores have hosted the magentocore[dot]net parasite during the full past six months," de Groot writes.
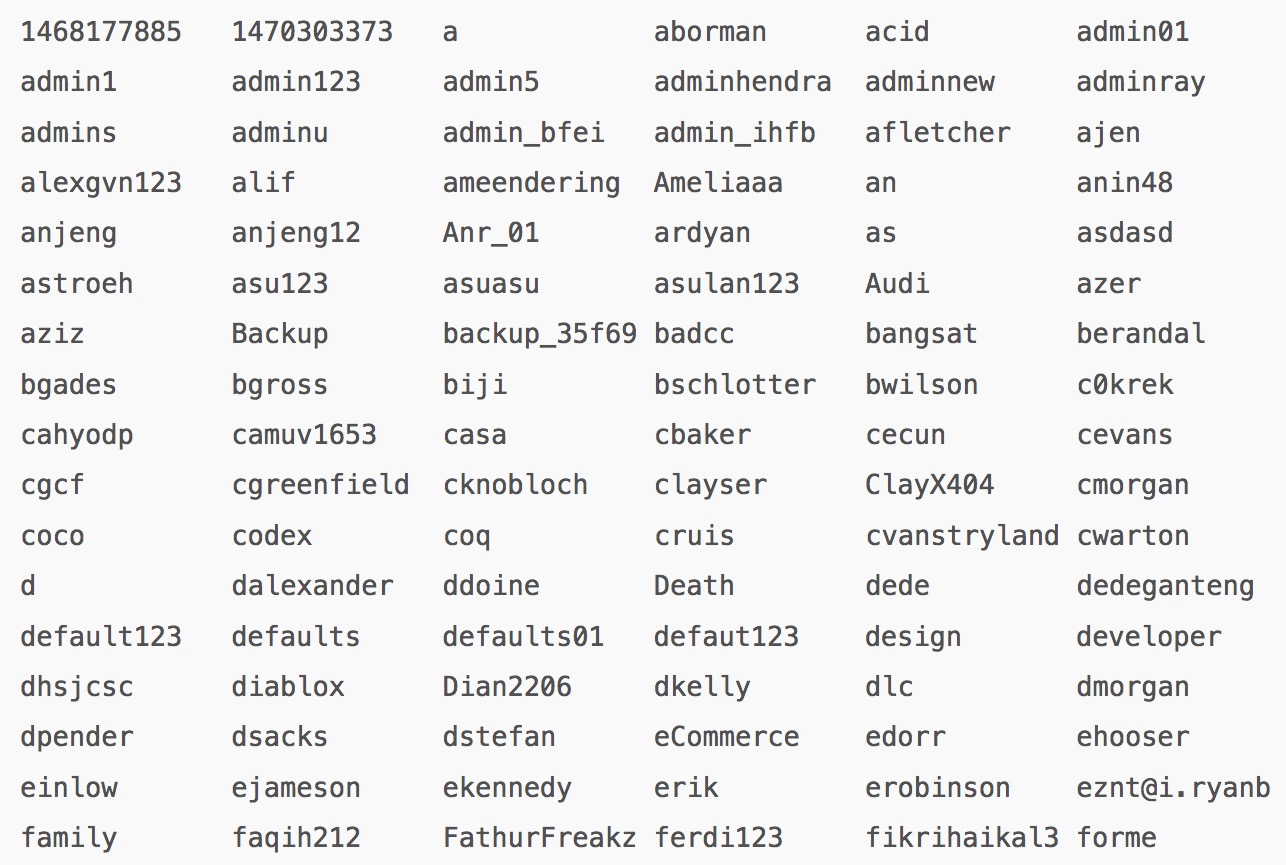
Attackers often execute a brute-force attack against a Magento control panel, de Groot says.
And attackers are clever: Their code can remove other malicious code that's already in a Magento installation and is also designed to hide its tracks. The malicious code does that via a backdoor included in a cron.php file placed by attackers periodically downloads "malicious code, and, after running, delete itself, so no traces are left," he writes.
The code also changes the password for registered Magento users to "how1are2you3," de Groot writes.
Shields Up
For combating these types of campaigns, de Groot says there are a number of best practices that Magento users should be following, and he notes there are free security tools that may be able to spot an infection. Access logs will also record abnormal activity, including after-working-hours activity, which security teams can use to spot outbreaks.
"If suspicious activity is recorded from staff IPs, it could be that a staff computer is infected with malware, or that the attacker has hijacked an authorized session," he writes.
Once the entry point has been closed, administrators need to find where the Magento code base has been altered. That process can be tricky, and de Groot writes that if all backdoors aren't found, potentially also hidden in innocuous-looking HTML or JavaScript, "you can start all over in a few weeks" after attackers return and pick up where they left off.

It's best to nuke infected installations and restart, he says. "Revert to a certified-safe copy of the codebase, if possible," de Groot writes. "Malware is often hidden in default HTML header/footers, but also in minimized, static JavaScript files, hidden in deep in the codebase. You should check all HTML/JS assets that are loaded during the checkout process."
De Groot's has published an open-source malware scanner for Magento on GitHub.
Another free scanning tool, MageReport, is run by Dutch IT services provider Byte. MageReport uses passive scanning to detect problems, so it can't see problems on the server itself. MageReport warns that there may be false positives or false negatives due to differences across Magento installations, so it should only be used as a guide.
Last October, Magento launched its own security scan tool, which checks patch levels and configuration issues and whether best security practices are followed. The tool runs on Magento Commerce, which was formerly named the Enterprise Edition, and Magento Open Source, formerly called the Community Edition.