Cybercrime , Electronic Healthcare Records , Fraud Management & Cybercrime
Bupa Fined $228,000 After Stolen Data Surfaces on Dark Web
Health Insurer Slammed by Regulator for Failing to Detect Bulk Theft of Records
The U.K.'s data protection regulator has fined Bupa Insurance Services £175,000 ($228,000) for failing to stop an employee from stealing 547,000 customer records, which were later offered for sale on the dark web.
See Also: The State of Organizations' Security Posture as of Q1 2018
The Information Commissioner's Office didn't hold back in its criticism of the health insurer. The ICO says that three months after the incident was discovered, Bupa had still failed to ensure that rogue employees couldn't exfiltrate personal data (see Insurer Bupa Blames Breach on Rogue Employee).

The records were extracted from Bupa's customer relationship management system, dubbed SWAN, which contained 1.5 million records. U.K. Information Commissioner Elizabeth Denham found that Bupa's inadequacies around SWAN "were systemic, rather than arising from any specific incident or incidents."
"Bupa Insurance Services Limited is a large, well-resourced and experienced data controller," according to the ICO's penalty notice. "It should have appreciated that the misuse of the relevant personal data was likely to cause substantial damage or distress."
The ICO found that Bupa violated elements of the U.K.'s Data Protection Act 1988.
The stolen customer data included names, birth dates, nationalities, policy-related data including membership numbers, email addresses, phone numbers and fax numbers. No medical data was stolen.
For Sale: 500,000 Records
An external partner notified a staff member of Bupa Global on June 16, 2017, that "customer data of an international health insurer was being offered for sale on the popular dark web site, AlphaBay Market," the ICO says.
AlphaBay was an online marketplace offering a variety of illegal goods, from fake IDs to stolen data to drugs. The site was taken offline in early July 2017 after a joint operation by law enforcement agencies from the U.S., Canada and Thailand (see Darknet Marketplace AlphaBay Offline Following Raids).
The employee placed an ad on the AlphaBay offering more than 500,000 records from a "well-known international blue chip medical insurance company," the ICO says, adding that the data came from Bupa customers in 122 countries.
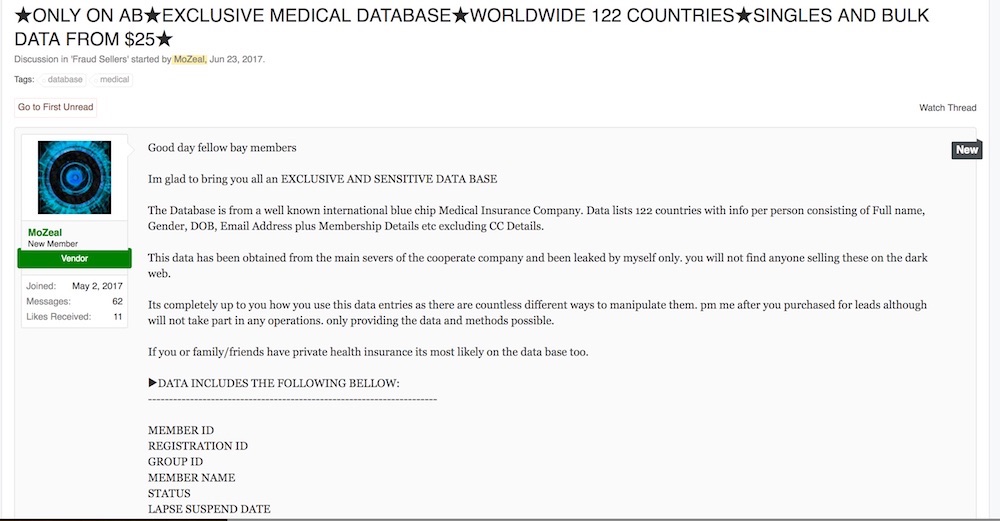
A sample of the data obtained by Bupa was "identical" to that held in SWAN, the ICO says.
The rogue employee, referred to as "AA" - as well as being male - in the penalty notice, was suspended on June 19, 2017. The individual worked in Bupa's Brighton office and was a member of the company's Partnership Advisory Team (PAT).
The PAT team, which had 20 members, had access to SWAN, as did 1,351 other users, according to the penalty notice. But the PAT team had sweeping access to the database and could run reports without restrictions.<.p>
SWAN reports "could then be downloaded and held on shared drives and personal drives in order to respond to broker enquiries on a 'first-time resolution' basis," the ICO says. "This illustrates the tension between customer satisfaction and information security."
Long-Running Breach
An investigation showed that AA had been dipping into Bupa's records starting as early as 2013.
Between December 2013 and January 2017, AA saved to his desktop three data sets that came from mandate forms. The data included credit card details for 15 people. AA also sent to his personal email account two Excel files containing the amounts of treatments and dates for 36 data subjects, the ICO says.
The biggest haul, however, came between Jan. 6 and March 11, 2017. During that time period, AA exfiltrated 547,000 customer records. He generated bulk data reports from SWAN and then zipped the files and attached them to six emails sent to his personal account.
"This was the data offered for sale on the dark web," the ICO says, although it notes there is no evidence that the data was actually sold.
Logging Problems
The ICO says that Bupa erred by giving so many people access to large volumes of data.
The "20 PAT members were also able to make searches, view large numbers of customers records at a time and export data to separate applications and files including file-sharing platforms and social media," the ICO says. "Those capabilities facilitated potential large-scale misuse of the relevant personal data over a short period of time. There was no adequate justification for those capabilities."
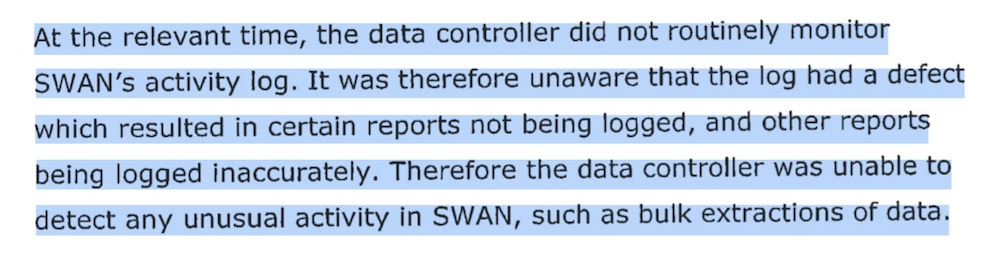
Bupa also failed at logging. The company, the ICO says, didn't monitor its logs, which made it unable to detect suspicious activity. Also, Bupa was unaware that its logging system had a defect "which resulted in certain reports not being logged, and other reports being logged inaccurately," according to the ICO.
Following the breach and the ICO's findings, Bupa has reached an agreement with the ICO that will see the insurer participate in an annual audit program. The ICO says Bupa has also "implemented certain measures to prevent the recurrence of such incidents."
Bupa can appeal the ICO's penalty within 28 days. If it pays the ICO by Oct. 26, the penalty will be reduced to £140,000 ($181,000).
The incident occurred before the EU's General Data Protection Regulation, which calls for tougher penalties, went into full effect earlier this year.