Fraud Management & Cybercrime , Next-Generation Technologies & Secure Development , Ransomware
Want to Get Into Ransomware? This Kit Costs Just $175
Karmen Ransomware Is Based on Open Source 'Hidden Tear' Code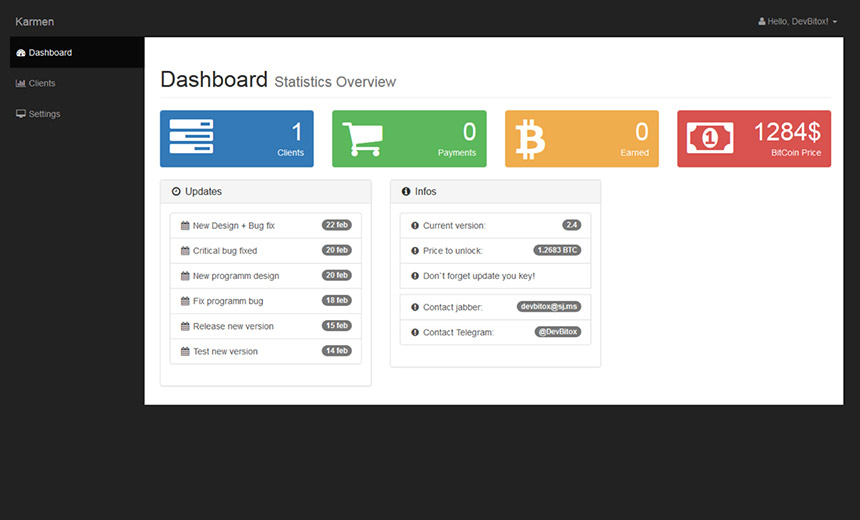
Ransomware has become one of the largest and most lucrative underground cybercriminal businesses, and like any venture, its purveyors continue to find new ways to innovate. To wit: researchers with threat intelligence vendor Recorded Future say a Russian hacker has cobbled together a low-end ransomware kit, called Karmen, that costs the unusually low amount of just $175. It's aimed at those wanting a piece of the cryptolocking ransomware action but who are not themselves coding geniuses.
See Also: The Cybersecurity Swiss Army Knife for Info Guardians: ISO/IEC 27001
File-encrypting malware has had a devastating impact on consumers and businesses alike, and it's estimated that such scams have generated at least tens of millions of dollars in illicit revenues. Victims must pay a fee - typically, in a cryptocurrency such as bitcoin - to receive a decryption key to unlock their files.
The FBI and other law enforcement agencies continue to advise victims to not pay ransoms, whenever possible, although the final decision is a victim's to make. Furthermore, paying can sometimes be the only way to recover files, absent an up-to-date backup, stored offline. Numerous universities and medical institutions, amongst others, have paid, saying they had little choice, and many such institutions are now reportedly stockpiling bitcoins as a potential "get out of jail" card should they fall victim in the future (see Hollywood Hospital Pays Ransom to Unlock Data).
Like many other aspects of the burgeoning cybercrime ecosystem, ransomware is becoming increasingly compartmentalized. About a year ago, for example, multiple information security firms clocked the emergence of ransomware-as-a-service, referring to easy-to-use kits that will run all aspects of a ransomware campaign.
Gateway Malware
The ransomware-as-a-service business model typically involves kits that can be used for free. Kit users, however, must pay a share of their profits to the kit's developers, Andrei Barysevich, director of advanced collection at Recorded Future, tells me.
But this business model has flaws. For starters, to avoid crackdowns, ransomware developers must vet potential users before sharing their tools. Even so, their carefully developed code sometimes found its way into the hands of information security analysts seeking better ways to detect and block it.
Recruiting new users is another challenge. Potential new recruits who are themselves newer, unproven members of cybercriminal forums often get locked out of such profit-sharing deals, since they will not have developed enough of a reputation to be trusted, Barysevich says.
Such business challenges have driven a new-ish approach, in the form of Karmen ransomware. And the low, one-off fee for the kit is in part what is raising eyebrows, since it dramatically lowers neophyte cybercriminals' barrier to entry.
Recorded Future, which monitors underground forums where cybercriminals trade tools, first spotted Karmen-related chatter in March. The code appears to have originated with a native Russian speaker who's likely based in in Belarus, Ukraine or Russia, and who goes by the nickname "DevBitox."
"Karmen is a gateway for newer members into the ransomware industry," Barysevich says. "There was this kind of like a void, a gap of supply. He probably realized there's a market."
Open-Source Moves
Part of the reason Karmen is so cheap is that DevBitox didn't develop the malware from scratch. Rather, it's a derivative of the Hidden Tear ransomware released by Utku Sen, a Turkish developer. Sen somewhat controversially published Hidden Tear in 2015 as open-source code for research purposes, although the project has since been abandoned.
Hidden Tear isn't as advanced as other ransomware, but it is effective. And DevBitox isn't the first one to use it to build ransomware designed to turn a profit (see Ransomware Gets Pokémon Go Treatment).
Luckily, there is already a free decrypter for any files that get locked with Hidden Tear, available via the No More Ransom portal.
Karmen does differ from Hidden Tear. Barysevich says DevBitox added a dashboard to manage ransomware campaigns, amongst other features. For example, DevBitox claims on an underground forum that the malware can automatically delete itself after a victim pays the ransom. Karmen also comes in two versions, a light and full version, the latter of which can also detect debuggers, virtual machines and sandboxes.
DevBitox has allegedly sold 20 copies of Karmen and is offering only five more before capping sales. At $175 a pop, that doesn't promise the developer a big payday. Barysevich, however, says that according to DevBitox's forum posts, the developer doesn't expect to make a lot of money. Furthermore, he also doesn't appear to be terribly interested in barnstorming the ransomware business.
Aiming for mass-market success can be a burden. Selling malware that remains undetectable to security products requires almost daily modifications, via a process called obfuscation or "cleaning." If DevBitox acquires too many customers, his service - and his reputation in the underground - might suffer, Barysevich says.
"It's impossible for him, with these prices, to sell it to a lot of people," he says. "If you sell it to a few hundred people, you'll be doing service and maintenance on copies that you sold, nonstop. He had to limit the number of copies that he is selling to find the perfect balance to support it and receive positive feedback from users."
Claim: 'Fully Undetectable'
Recorded Future hasn't yet secured a copy of Karmen, Barysevich says, but it is trying. It's also not clear how many people have been infected with this ransomware variant, or how it's designed to spread.
DevBitox's advertisement claims Karmen is FUD, short for fully undetectable, which is the term applied to malware that can slip past any security software or other anti-malware defenses. Whether that is true is impossible to verify. But DevBitox has shown that there's room in the lower-end market for ransomware tools, and that economic reality doesn't bode well for consumers and organizations.











