Governance & Risk Management , Next-Generation Technologies & Secure Development
MacKeeper Hid Product Update Error
Security Software Wasn't Receiving Updated Anti-Virus Signatures
Most anti-virus applications depend strongly on regular updates that supply technical descriptions of new malware, known as signatures. Although signatures aren't the only way to detect malware - some vendors are moving away from using them - they're useful for stopping viruses, albeit after an attack has been seen in the wild.
See Also: The Cybersecurity Swiss Army Knife for Info Guardians: ISO/IEC 27001
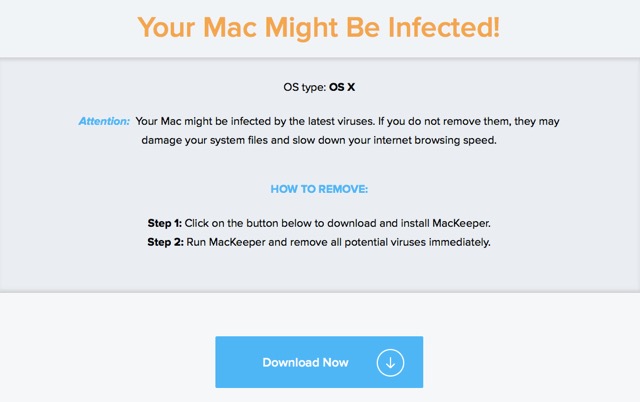
Enter MacKeeper, a security product for Apple computers whose annoying pop-up advertisements warning "Your Mac Might Be Infected!" abound across the web. MacKeeper, owned by Kromtech Alliance Corp. of Germany, has long been criticized for its marketing techniques.
Earlier this month, AV-Test, an independent anti-virus testing organization, released the results of an evaluation of a dozen Mac security products. It intended to test MacKeeper, but the software was dropped after it was found to not be updating itself. AV-Test says it was told MacKeeper, which licenses an anti-virus engine from Avira, had problems receiving updates for three months.
Having written about MacKeeper several times last year as its former owner was reacting to a class-action lawsuit that centered on alleged deceptive marketing practices, I decided to query Kromtech.
It's Not Us, It's Avira
Bob Diachenko, a senior PR expert with Kromtech, blamed Avira, saying a 32-bit file the company delivers to update MacKeeper's signature database was misconfigured. He said the issue didn't last three months, but between four to six weeks. I then reached out to an Avira spokeswoman, who told me that the problem, which didn't affect other Avira products, was resolved in May.
Six weeks seemed to me to be a long time for a security product to not receive signature updates. To be sure, far fewer malware programs target Apple Macs as compared to Windows. This year, there have only been about three true Mac malware programs (see Alert: Ransomware Targets Macs). But Mac security software often does flag so-called potentially unwanted programs such as adware, of which there have been a few dozen samples and variants circulating this year.
I asked Kromtech's Diachenko if his company notified its customers of the product error. "[The] AV database was outdated only for the mentioned period of time, so we did not notify our customers taking into account the temporary character of the issue," he says.
Simon Edwards, founder of the security software tester SE Labs in London, says that in the early 2000s, AV products would get updates weekly, but those days are long gone.
"I'd say that even a week was quite a long time in the world of anti-malware updates," Edwards says. "I would be very disturbed to learn that my anti-malware solution was quietly failing to download updates for any length of time."
Maik Morgenstern, CTO for AV-Test, says the risk to Mac users would be lower than if the same sort of glitch occurred with a Windows AV product. But still, the lack of notification to customers of a product fault smacks of irresponsibility.
"Any disruption in the service should be reported to the user," Morgenstern says.
Questionable Detection
Since Kromtech acquired MacKeeper in April 2013, it has sought to rehabilitate its image, toning down its marketing and tweaking warnings it presents to potential customers who stumble across its ads. As part of those efforts, it has sought to position itself as a peer of other security companies, and in January it launched an Analytical and Security Center run by Chris Vickery.
Vickery was retained about a month after he discovered a 21GB MongoDB database containing Kromtech's customer data online that required no authentication to view (see MacKeeper: 13M Customers' Details Exposed ).
But Kromtech would probably be best served by directing its research efforts toward its own product.
As part of research for this blog to figure out if MacKeeper had resumed getting updates, Thomas Reed, a Mac security expert who now works for Malwarebytes, took a look at MacKeeper version 3.10.1 running on Mac OS X 10.10.5.
Reed installed "Eleanor," the nickname for a backdoor discovered earlier this month that was seeded inside a fake file converter called EasyDoc Converter (see Mac Malware: Still No Need to Panic). MacKeeper detected a couple of PHP files associated with Eleanor but not the launch agents or executables.
"Eleanor should still work just fine in this state," Reed says.
The fault, though, lies with Avira, since MacKeeper licenses its AV engine. For reference, Reed tested Avira's engine against Eleanor and achieved the same result - the malware wasn't detected.
The lesson here from all of this isn't anything new: Be wary of MacKeeper and Avira.











