Fraud Management & Cybercrime , Next-Generation Technologies & Secure Development
Mac Malware Targets Biomedical Institutions
'Fruitfly' Targeted for Eradication via Apple macOS Update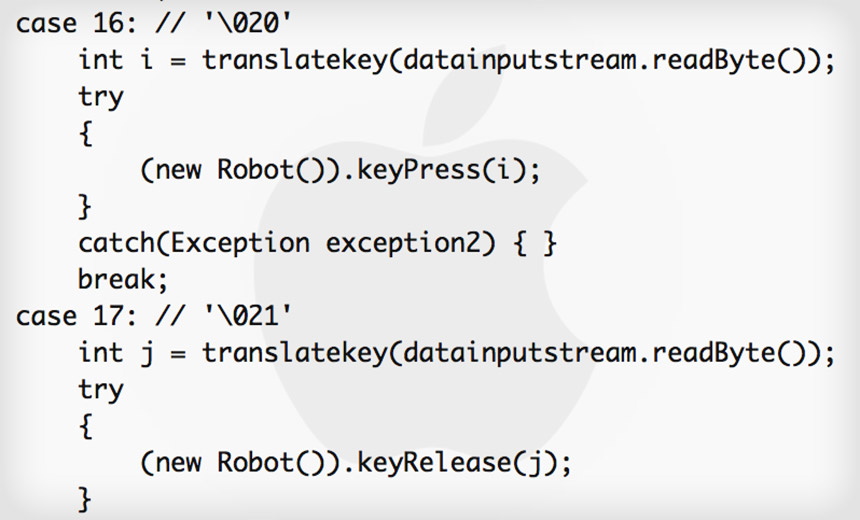
For the most part, hackers don't put a lot of effort into attacking Apple's operating system. It's not that the macOS lacks vulnerabilities. But Microsoft still dominates the desktop market, meaning attackers can catch plenty more fish by targeting Windows (see Mac Malware: Still No Need to Panic).
See Also: The Cybersecurity Swiss Army Knife for Info Guardians: ISO/IEC 27001
Even so, a researcher has cracked open what appears to be the first piece of Mac malware for the year, and it's a curiosity thanks to employing some very old code, as well as the specific types of victims it seeks.
Fortunately, the malware in question - designed to take screenshots and gain access to webcams - is easy to detect and remove. But it's already been circulating for at least two years, writes Thomas Reed, a researcher with anti-malware software vendor Malwarebytes whose job includes analyzing malware that targets Apple machines.
Reed first got a heads-up on the malware thanks to an IT admin who saw odd network traffic originating from a Mac. "This led to the discovery of a piece of malware unlike anything I've seen before, which appears to have actually been in existence, undetected, for some time, and which seems to be targeting biomedical research centers," he says.
Say Hello to Fruitfly
Malwarebytes calls the malware Quimitchin, which is the name for Aztec spies who would infiltrate other tribes. Apple, meanwhile, has dubbed it Fruitfly.
Fruitfly contains functions and system calls that predate OS X - Apple's major rewrite of its operating system that debuted in 2001. Reed writes that the malware also employs a code library called libjpeg, which is used for encoding and manipulating JPEG images. But the library, as implemented in Fruitfly, hasn't been updated since 1998.
Reed has a couple of theories behind attackers using the old code. He says that it could "signify that the hackers behind it really don't know the Mac very well and were relying on old documentation. It could also be that they're using old system calls to avoid triggering any kind of behavioral detections that might be expecting more recent code."
Reed tells me that it's unclear how Fruitfly gets installed on Macs, and as of yet, no one has recovered related "dropper" or installation code. As a result, Apple can't update the anti-malware application built into OS X, called XProtect, to prevent the malware from being installed.
But on Jan. 18, Apple did release a related update for the malware removal tool built into macOS, Reed says.
Another distinguishing feature is that Fruitfly will also run on Linux and has shell commands for that OS. "This suggests that there may be a variant of this malware that is expressly designed to run on Linux, perhaps even with a Linux executable in place of the Mach-O executable," Reed says. "However, we have not found such a sample."
Biomedical Targets
Reed theorizes that Fruitfly stayed under that radar for so long because it was only used in very targeted attacks. He tells me that it has infected several biomedical institutions in the United States, but could not reveal their names.
"There's been a lot of talk in the last few years about China stealing scientific data from U.S. and European countries, and this is what it seems like, but there's no evidence at this point connecting to China," he says. "It could easily be someone else."
Fruitfly communicates with two command-and-control servers. Reed says Malwarebytes found two other types of Windows malware that spoke to the same servers. Unfortunately, there's not a lot of readable text in Fruitfly's code that might shed light on which individuals or group authored it.
The good news however, is that Fruitfly will no longer lurk in the shadows.











