DDoS Protection , Fraud Management & Cybercrime , Governance & Risk Management
Free Source Code Hacks IoT Devices to Build DDoS Army
But Code Release Offers No Free Lunch for Cybercrime Script Kiddies
Bad news: A hacker has released source code for malware that can be used to automatically find and hack internet of things devices that use default accounts and passwords, then use them to launch distributed denial-of-service attacks. Numerous Linux-based routers, security cameras and digital recorders, among other devices, are at risk and have been compromised in this manner to unleash record-breaking attacks (see Hacked IoT Devices Unleash Record DDoS Mayhem).
See Also: The Cybersecurity Swiss Army Knife for Info Guardians: ISO/IEC 27001
Good news: Using the attack code isn't as simple as clicking "compile," meaning that unskilled "script kiddies" may find themselves hard-pressed to create an army of hacked IoT devices ready to do their DDoS bidding.
More bad news: It's a virtual certainty that the leaked code will be widely used, as well as eventually refined and turned into point-and-click attack tools for less technically sophisticated DDoS attackers.
Those are just a few of the takeaways following malware developer "Anna-senpai" releasing for free the supposed source code for Mirai malware, which has been tied to massive DDoS attacks launched via hacked IoT devices.
The source code dump was announced by Anna-senpai Sept. 30 in a post to Hack Forums, a social network devoted to hacking that security experts say attracts numerous hacker wannabes - a.k.a. script-kiddies - who lack technical knowledge but want to know how to bolster their skills. Many cybercrime-as-a-service purveyors advertise their wares on the site.
"Just so it's clear, I'm not providing any kind of 1 on 1 help tutorials," Anna-senpai said, noting that configuring the related scripts should take someone who knows what they're doing less than one hour.
Some security experts say the Mirai botnet appears to be the one that deep-sixed the website of information security journalist Brian Krebs, who ironically was also the first to report on the subsequent source code release. The malware targets Linux systems' SSH or telnet accounts, according to an analysis of the Mirai botnet published by the group of security researchers who are part of the "Malware Must Die" team.
The security researcher known as "Hacker Fantastic," via Twitter, rates the Mirai code "5/10, easy on the eyes, well commented, not an innovative malware but would read again. A++" and says it's designed to disrupt sites via UDP, TCP, DNS, GRE and HTTP attacks.
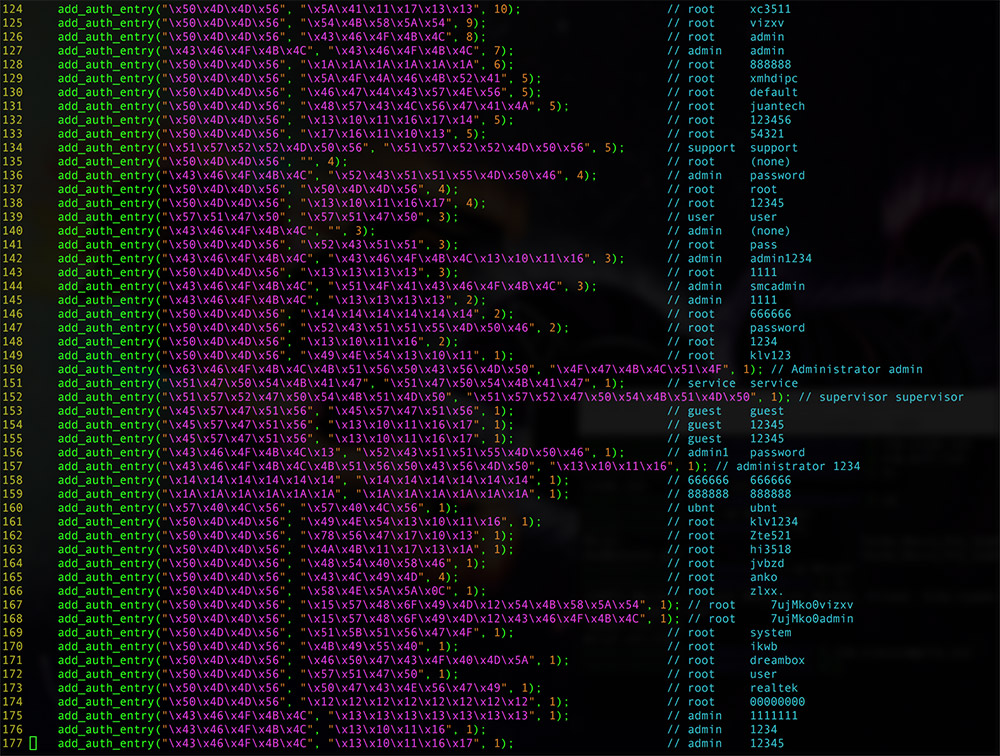
Thankfully, getting the code to work requires some technical knowledge. "The Mirai source code appears to be legitimate, but has been modified to mess with scriptkiddies who just compile and run," the security researcher known as Malwaretech says via Twitter.
Anna-senpai claims to now be giving up the DDoS thug life. "When I first go in DDoS industry, I wasn't planning on staying in it long. I made my money, there's lots of eyes looking at IOT now, so it's time to GTFO," Anna-senpai's post reads. "So today, I have an amazing release for you. With Mirai, I usually pull max 380k bots from telnet alone. However, after the Kreb [sic] DDoS, ISPs been slowly shutting down and cleaning up their act. Today, max pull is about 300k bots, and dropping."
Stresser/Booter Options Abound
DDoS attacks and related tools have long been sold via cybercrime sites by groups such as Lizard Squad, often labeled as stresser/booter services.
But Mirai is just one type of malware designed to compromise IoT devices. "We're thinking this is the tip of the iceberg," Dale Drew, head of security at Level 3 Communications, told The Wall Street Journal.
Level 3 operates one of the world's biggest backbones, thus giving it insight into network traffic. It says a notable number of recent DDoS attacks appear to be getting launched via compromised devices - especially security cameras and digital video recorders - built by Chinese manufacturer Dahua Technology. The company's technology is often re-branded and sold by other companies; its website lists dozens of technology partners in the United States alone.
Dahua Technology didn't immediately respond to my request for comment on those reports. But a spokeswoman told The Wall Street Journal that it's reviewing Level 3's research, noted that older devices running outdated software could be easy prey and recommended users set a password on the devices as well as upgrade the firmware.
If all it took to create biggest recorded DDoS attack in history was a telnet scanner and 36 weak credentials the net has a huge IoT problem
— Hacker Fantastic (@hackerfantastic) October 3, 2016
Socialism for IoT-Built Botnets
In August, Level 3 reported that it had detected that 1 million IoT devices built by Dahua Technology had been infected with malware called Bashlite - a.k.a. Lizkebab, Torlis, Gafgyt - which is also used to generate DDoS attacks. Together with cybersecurity firm Flashpoint, Level 3 said it was tracking more than 200 related command-and-control servers, which are used to send and receive instructions to hacked devices. Some C&C servers, it added, launched up to 100 attacker per day.
Today, any would-be attackers can tap Bashlite malware. "The source code for this malware was leaked in early 2015 and has been spun off into more than a dozen variants," according to a blog post from Level 3's threat research labs.
No doubt the same will now happen with Mirai source code.
If there's one upside, however small, it's that at least one solo hacker no longer controls thousands of compromised devices, MalwareTech says via Twitter. "Nice thing about the [Mirai] code being public is it mean less devices for any single person to control .... kinda like socialism for botnets."