3rd Party Risk Management , Breach Notification , Business Continuity Management / Disaster Recovery
Australian Government Staff Data Leaked in 3rd-Party Breach
Ransomware Group, Believed to Be Conti, Exfiltrated Data of 38,000 Employees
A Nov. 16 ransomware attack on Frontier Software leaked "significant personal information" of thousands of South Australian government employees on the dark web, according to a Friday statement by Rob Lucas, treasurer of South Australia.
See Also: Take Inventory of Your Medical Device Security Risks
Lucas referred to a Thursday update by the software company, whose HR and payroll system Chris21 had been attacked. The update says that state government data had been stolen from its network during the incident and published on the dark web.
Frontier Software at the time of the incident assured customers that "to date, our investigations show no evidence of any customer data being exfiltrated or stolen." It said that the Australian customer HR and payroll data and systems were segmented from the corporate systems and had not been compromised.
But an investigation by cybersecurity experts from CyberCX - onboarded by Frontier Software in November - revealed that data had been exfiltrated from Frontier Software's internal Australian corporate environment.
What Was Leaked?
Frontier Software has been undertaking payroll services on behalf of the South Australian Government since 2001, says Lucas. "Records of at least 38,000 employees were accessed, and up to 80,000 employees might have been accessed" by the ransomware actors, he says. The government, he adds, will soon establish a more accurate number.
The illegally accessed data, according to Lucas, contains details such as first and last names, date of birth, tax file number, home address, bank account details and remuneration, tax withheld, payment type, lump sum payment type and amount, superannuation contribution, and the reportable fringe benefits tax of the government employees.
South Australian Premier Steven Marshall may be among those affected, news agency ABC News reported, citing Lucas.
Both Lucas and the South Australian Government did not specify the departments whose data had been leaked, but confirmed that no Department for Education employees had been affected, as they do not use Frontier Software for payroll services.
An emergency cybersecurity update released by the South Australian government on Friday shows that public sector employees and people on the state government's payroll, including the Australian Taxation Office, Services Australia, Super SA - the public sector employee superannuation scheme, financial institutions, Maxxia - the South Australian Government’s salary sacrifice provider, and employee unions, were alerted about the breach.
Attribution
Neither CyberCX nor Frontier Software responded to Information Security Media Group's request for information on the attacker's identity.
ISMG's review of a post by Conti ransomware group on its data leak site - Conti News - shows that the threat actor may be responsible for the attack. The data leak site shows 10 [.]rar files, allegedly comprising 3.75 GB, or 10%, of Frontier Software data, up for sale.
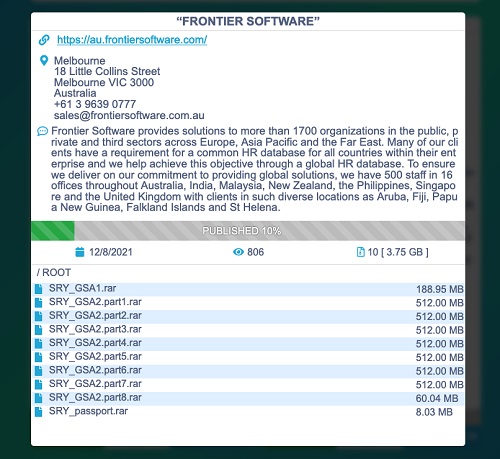
The post has since been deleted, raising speculation about whether a ransom had been paid - despite the Australian government's "no ransom payment" approach - or whether the data had been sold.
Response Plan
Frontier Software, in its November update, said it had tightened its security perimeter by actively monitoring all environments with the help of CyberCX security experts.
Lucas, in his latest statement, says that the South Australian Government has partnered with cybersecurity support service IDCARE, a nonprofit organization that specializes in identity theft and crisis management, to develop a specific response plan and offer affected employees personal support throughout the process.
The government should have a more robust testing and audit program in place to ensure that all third-party software is secure, Ciaran Byrne, head of platform operations at cybersecurity firm Edgescan tells ISMG. He says that wherever it makes sense, it's advisable to keep certain elements in-house.
"As easy as it is to say that everyone should develop their own software to take care of their own data, it’s not practical and would be sure to introduce more security issues in the long run than relying on tried and trusted third parties who should have more expertise in building software in their specific fields," he says.
The key is to pick the right provider, keep software up to date, and ensure it is administered correctly, Byrne says.
The incident has yet again shown the importance of prioritizing supply chain security, Aaron Bugal, global solutions engineer for the Asia-Pacific and Japan region at cybersecurity firm Sophos, tells ISMG.
"It is not enough for organizations to just focus on their own security infrastructure; they must understand and have confidence in the security of their entire supply chain. Regardless of whether supply chains exist in physical or digital channels, they must be included within risk modelling and incorporated into an incident response plan, as they are an extension to the business."