Events , Governance & Risk Management , Incident & Breach Response
Asia Needs Resilient Cyber Defense
Security Leaders Respond to RSA President's Keynote Address
Amit Yoran, president of RSA, the security division of EMC Corporation, urges South East Asian organizations and governments to re-think their traditional approach to security in building a resilient cyber defense mechanism. Saying they should move beyond breach prevention and reaction, he outlines five principles for evaluating a next-generation approach relying on detection and effective response mechanisms.
See Also: Digital Evolution and Fraud Evolution: How to Keep Up with the Changing Times
Yoran shared his thoughts as the keynote speaker at the launch of RSA Conference Asia Pacific & Japan, in Singapore, on how the game has changed and it's time to gear up.
"Breaches of the past couple of years show that the way our industry has been doing security isn't working," Yoran says. "The adversary continues to get through even 'next-generation' defenses and what's worse, goes undetected for months or even years."
In response, cybersecurity leaders in attendance welcomed Yoran's views around the perimeter continuing to dissolve under the onslaught of mobile and cloud technologies. However, they outline the challenges facing Asia Pacific enterprises in building a robust security framework.
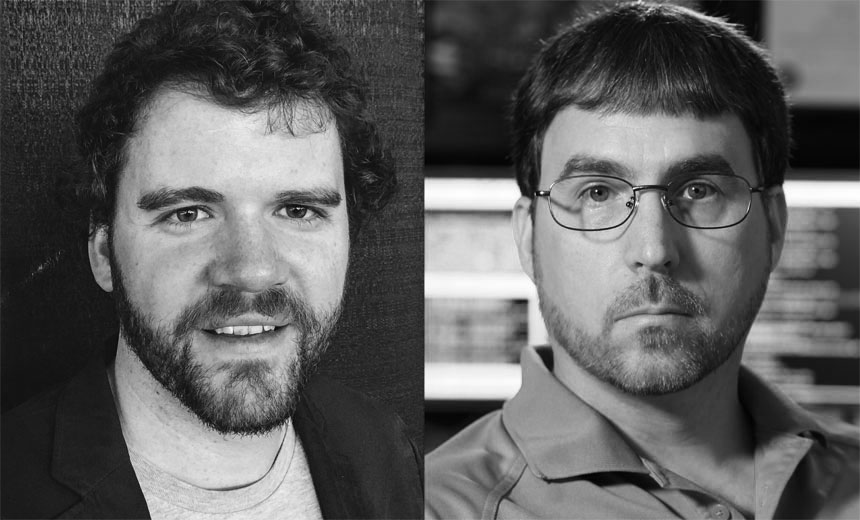
Australia-based Wayne Tulek, IT security architect at Officeworks, says the key challenge is about people, process and technology - not about investing in security.
"Most top enterprises in the west invested millions, yet witness breaches," Tulek says. "Breaches revolve around people who don't do the right things: it's key to address policies and people."
The Game Change
Yoran laid emphasis on enterprises realizing the game has changed, and the only way out of the vicious cycle of prevention and remediation is changing their mindset.
"The industry is still selling the perimeter as the primary line of defense," he says. "Beyond that irrational obsession, some follow an equally absurd path to detecting advanced threats."
The threats that matter most today are those many haven't seen before, Yoran says. Today's tools cannot detect these advanced threats that cause the most damage.
"It may've been a shock to [security leaders] when last year's Verizon Data Breach Investigations Report asserted that SIEM systems spotted less than one percent of successful advanced threat attacks," Yoran says. "Less than one percent. The game has changed, but so many still cling to selling the stamps we're so comfortable with."
Building Resilient Defense
Yoran recommends five principles to navigate the digital landscape:
- Accept that even advanced protections are insufficient for today's threats - No matter how high or smart the walls, focused adversaries will find ways over, under, around and through.
- Visibility from the endpoint to the network to the cloud is necessary - The single most common and catastrophic mistake is under-scoping an incident and rushing to clean up compromised systems before understanding the broader campaign.
- Effective management of identities matters more than ever - In a world with no perimeter and fewer security anchor points, identity and authentication matter more than ever. The abuse of identity is a stepping stone attackers use to impose their will.
- Organizations must leverage external threat intelligence - Threat intelligence should be machine-readable and automated for increased speed and leverage. It should be operationalized into your security program and tailored to your organization's assets and interests, so that analysts can quickly address the threats that pose the greatest risk.
- Security programs must be guided by an understanding of risk - CISOs must understand what matters to their business and what's mission-critical. You have to defend what's important and defend it with everything you have.
"If one must build a resilient cyber defense mechanism, stop being a gatekeeper and think business-centric," Yoran says. "To be business-centric, involve business owners early and often. Give them control over the lifecycle and privileges of identities...give the right people access to the systems, applications and data they need, and it can be done."
Reactions from Cybersecurity Leaders
Security leaders and practitioners in attendance at RSA Conference resonated with Yoran's views.
However, they say organizational bottlenecks impede effecting the necessary changes.
The key concern of R Rajagopalan, manager-Critical Incident Response Centre at EMC Software and Services India Private Ltd., is insufficient training of teams across enterprises in APAC, as top managements fail to understand the importance of security and incident response.
"Before even thinking about technology or budget, it's critical to build awareness," he says.
Bill Taylor-Mountford, vice president & general manager-APJ at LogRhythm, says that the fundamental success of a resilient defence mechanism revolves around the security intelligence platforms used in the right manner.
'Spending is not enough; there's a shortage of skills even to detect the bad guys and their activities - a big concern," Taylor says.
Bangalore-based Bikash Barai, co-founder, iViz, a penetration testing and application security firm, welcomes top security leaders evangelizing the importance of the incident response mechanism. Barai says change is a top-down approach. "Most US enterprises see a top management buy-in building the wherewithal around security," he says. "Not so in APAC, as higher managements are less sensitive to security."
Yoran appreciates the challenges and referenced them in his remarks.
"I'm not saying we have all the answers; there are resource challenges, skill gaps and legal impediments," Yoran says. "But we are on the path to changing a paradigm under which our industry has operated for decades."
Additional Summit Insight:
Hear from more industry influencers, earn CPE credits, and network with leaders of technology at our global events. Learn more at our Fraud & Breach Prevention Events site.