Cybercrime , Endpoint Security , Fraud Management & Cybercrime
5 Malware Trends: Emotet Is Hot, Cryptominers Decline
Attackers Dig Deeper Into Businesses as WannaCry Lingers, Ransomware Lives On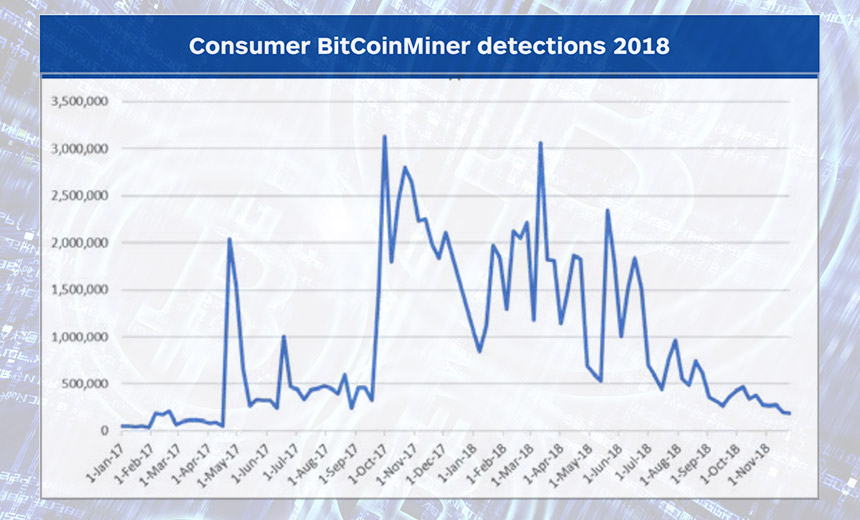
During 2018, Emotet malware, followed by a backdoor called Vools that can also drop malware onto infected systems, were the top two pieces of malicious code found on business systems, says security firm Malwarebytes in its new 2019 State of Malware (PDF) report.
See Also: Cybersecurity for the SMB: Steps to Improve Defenses on a Smaller Scale
The country that logged the most business system infections was the United States, followed by Indonesia, the United Kingdom, France and Malaysia, according to the report.
Here are five of the top findings from the report, which looks at malware trends from January to November of last year.
1. End of the Cryptocurrency Gold Rush
Starting in late 2017, many malware-using crime gangs dropped everything to focus on cryptocurrency miners, which steal CPU cycles to generate new cryptocurrency (see: Cybercriminals Go Cryptocurrency Crazy: 9 Factors).
As the value of cryptocurrency continued to rise or remain high, so did criminal interest in mining. "It was an amazing time for them to be spreading miners," Adam Kujawa, director of Malwarebytes Labs, tells Information Security Media Group (see: Malware Moves: Attackers Retool for Cryptocurrency Theft).
But by the middle of 2018, as the bottom fell out of the cryptocurrency market, attackers began to look elsewhere.
"We expect that the crypto craze, for now, is over, though there is still some drive-by mining," Kujawa says. "It seems like most cryptocurrencies have lost value, and thus a lot of criminals have lost their interest in mining them."
While infecting individual consumers with cryptocurrency mining malware appears to be losing its business value, he predicts that attackers will continue to push cryptominers onto servers and internet of things devices.
2. Can't Stop WannaCry
Throughout 2018, WannaCry remained one of the top pieces of malware seen in the wild, especially infecting organizations in the education, manufacturing and retail sectors, Malwarebytes says.
WannaCry burst onto the scene when it infected more than 300,000 computers worldwide in May 2017 using an exploit called EternalBlue that had apparently been stolen or leaked from the U.S. National Security Agency. The exploit was released by a group calling itself the Shadow Brokers. It took advantage of a Windows vulnerability, designated CVE-2017-0144, in Microsoft Server Message Block protocol version 1, which remained widely unpatched when WannaCry hit.
Even before WannaCry attacks spread, however, other malware, including cryptocurrency miners, had already seized on the vulnerability to spread, and they continued to do so last year (see: Wielding EternalBlue, Hackers Hit Major US Business).
"WannaCry is still a top detection, because it's still wandering around the internet," Kujawa says. "It doesn't do anything - this version doesn't encrypt anything; it just finds other systems to infect, and then it infects it and moves on. Worms are hard to kill."
3. Trickbot and Emotet Get New Tricks
Several security firms have said that in 2018, Emotet was the most-seen piece of classic malware, compared to cryptocurrency mining malware, fileless attacks or ransomware.
Carbon Black, for example, says the classic - aka commodity - malware it most often saw last year was Emotet, followed by GT32SupportGeeks, Swrort, Injector Trojan and the Donoff dropper. Separately, Check Point Software Technologies says Emotet was the most seen piece of classic malware at the end of last year (see: Emotet Malware Returns to Work After Holiday Break).
A one-time banking Trojan, Emotet has been upgraded to do more than just log keystrokes. Now, it can also "drop" - install - other malware, as well as turn endpoints into spam cannons. "Since Emotet takes over victim email accounts, malicious emails appear to come from trusted sources to their recipients," Malwarebytes says.
Today's more advanced version of Emotet typically uses spam to spread itself, sending emails that have an attached malicious Microsoft Word document with macros or which contain links in the email body to malicious URLs.
If Emotet infects a system, however, it then uses EternalBlue to exploit systems running vulnerable versions of SMB_v1. "Infected machines attempt to spread Emotet laterally via brute force of domain credentials, as well as externally via its built-in spam module," Malwarebytes says in its report. "As a result, the Emotet botnet is quite active and responsible for much of the malspam we encounter."
Trickbot spreads in a manner similar to Emotet - via malicious spam - when it's not installed by Emotet itself, Kujawa says.
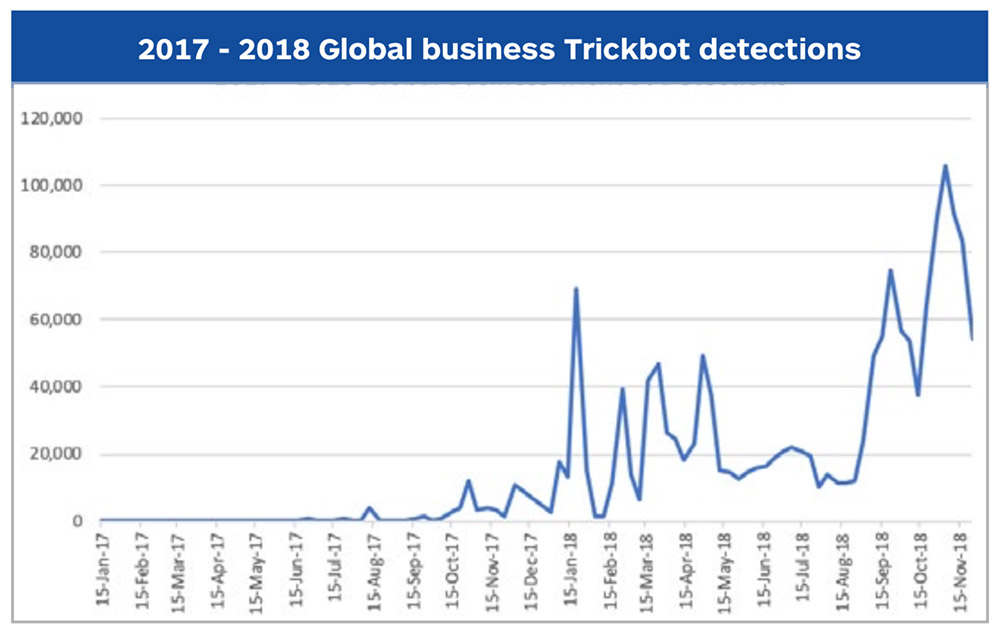
If Trickbot gets inside a network, it then uses another attack tool leaked by Shadow Brokers called EternalRomance, which also targets SMB_v1, to try to spread laterally.
4. Attackers Escalate Selected Infections
Another unexpected takeaway from last year, Kujawa says, is that some types of malware, including Emotet, infected consumers and business users at almost equal rates. That's unusual, because any given strain of malware has historically infected many more consumers than businesses.
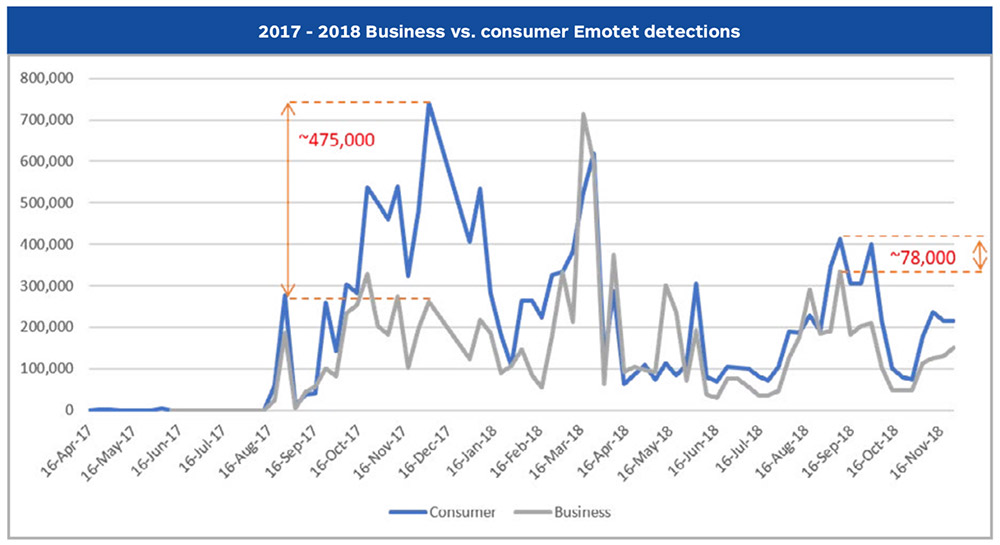
"Around September 2018, the consumer and business detections for Emotet matched up, which is very weird - we usually see way more of one than another," Kujawa says. "That means there's clearly targeting going on."
Attackers have been using Emotet as a dropper for other malicious code too, including Trickbot and IcedID.
Trickbot, meanwhile, has been used to push Ryuk ransomware onto infected systems. "Ryuk infections are seldom, if ever, dropped directly by Emotet, security firm Kryptos Logic reports. "When the Ryuk module is delivered to a victim, it is done transiently through a Trickbot infection and other tools, not the original Emotet bot."
CrowdStrike estimates that the group behind Ryuk, which it calls Grim Spider, has earned at least $3.7 million in ransomware payments since last August.
Kujawa says that attackers appear to be reviewing who their malware has infected and then escalating the attack - for example, by pushing Ryuk - if the target looks potentially lucrative.
"Now they're focusing their efforts a little more, going after these businesses, and once they land, they're able to expand very quickly throughout the network and get a foothold," he says. "As we saw from the Ryuk ransomware attack, clearly, there's some sort of either background observation [or] investigation into who the victims are of Emotet, because the Ryuk ransomware didn't hit every single infected Trickbot system in the world - it only hit a few."
5. GandGrab Looks Beyond Bitcoin
On the ransomware front, business-targeting SamSam and Ryuk infections might make headlines, but Kujawa says they are very rare, and the overall quantity of ransomware infections declined markedly from 2017 to 2018 as attackers focused more on miners (see: Suspected Ransomware Outbreak Disrupts US Newspapers).
"GandCrab is making the most noise, but it's not a lot of noise," he says, noting that it mostly targets consumers. In 2018, it was also notable for being the first big piece of ransomware to demand payment in a cryptocurrency that wasn't bitcoin (see: GandCrab Ransomware: Cat-and-Mouse Game Continues).
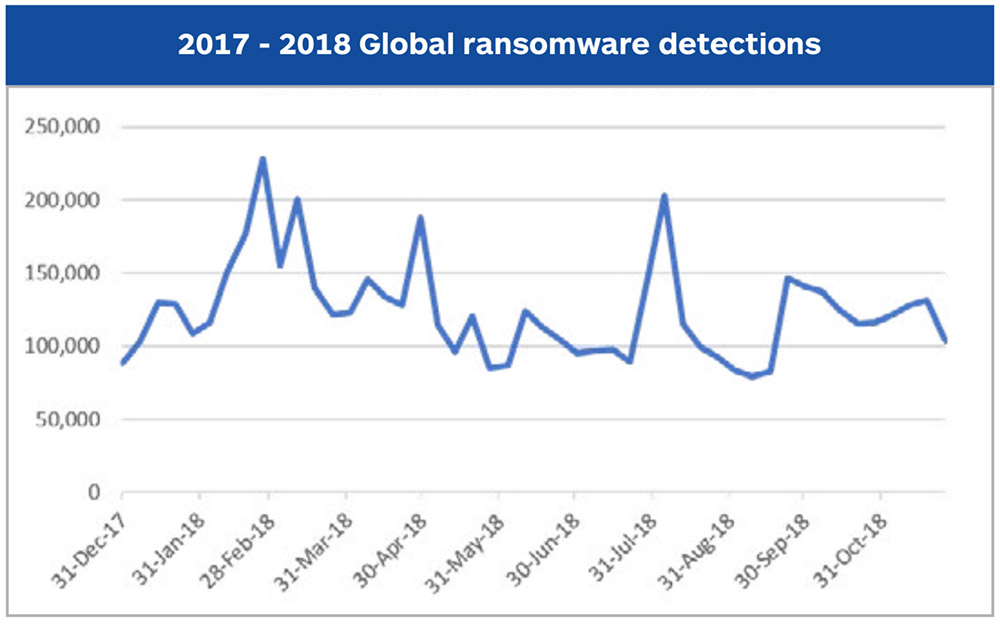
Even so, Malwarebytes expects ransomware infections to continue, with attackers attempting to find innovative new ways to distribute their crypto-locking code, as well as to make their encryption tougher to break.
GandCrab, in particular, remains a top threat because of its ability to not just encrypt PCs but also network shares, having also recently gained the ability to automatically map network shares, Kujawa says. "It also uses some pretty serious RSA encryption, so it's not just some cheap junk, like in the first version," he says. "It's definitely now a far more difficult encryption scheme to crack."