Data Loss Prevention (DLP) , Next-Generation Technologies & Secure Development
Refined Ransomware Streamlines Extortion
New CryptoWall, Crypto Tricks and Leak Threats
Cybercriminals are continuing to refine their ransomware tools and attack techniques.
See Also: Cybersecurity for the SMB
Notably, the gang behind notorious CryptoWall ransomware, which has been tied to at least $325 million in criminal proceeds, has released an updated and more streamlined version of their data-encrypting malware, and more than doubled the ransom they demand to decrypt infected PCs.
To compel more ransomware victims to pay up, meanwhile, the attackers behind a different type of ransomware called Chimera have been threatening to publicly dump stolen data from victims whose PCs they have encrypted.
Other recent ransomware advances include improved encryption techniques, to make it tougher to decrypt encrypted files without paying a ransom. To foil the efforts of security researchers to crack the encryption used on ransomware-infected PCs, for example, the developer behind Ransomcrypt.U has updated the malware to no longer transmit the encryption key to the attacker's command-and-control server.
Ransomware Gets New Crypto Tricks
RansomecryptU was first spotted in the wild in June 2014 on Russian-language cybercrime forums, and has since been updated about a dozen times, researchers at security firm Check Point say in a Nov. 4 blog post.
In the latest version of Ransomcrypt.U, "the encryption functionality is built with several layers of encoding and encryption, including two separate levels of RSA," they say, adding that they anonymously reached out to the attacker's email address "and received a reply requesting a payment of 20,000 Russian rubles ($315) on the same day or 25,000 ($390) on the following day, to receive a decryption program and key."
To date, only Russian language versions of the malware have been seen in the wild, security researchers say. "The Trojan changes the desktop wallpaper to display the ransom warning," according to an overview of the malware published by Symantec. "The message tells the user that their files have been encrypted and advises them to send an encrypted file to the attacker's email address. It says that if the user doesn't send a file within one week, then they won't be able to decrypt their files."
Unusually, however, the ransomware - also known as Ninja, VB-IHK and VBKryjetor - now encrypts the data "using three hardcoded RSA 768 public keys that the offender created in advance" and bundled with the malware. That means that the remote private keys - required to unlock the encrypted files - reside exclusively with the attacker, thus making them impossible to intercept.
"Most known ransomware must connect to the C&C server before performing encryption," the Check Point researchers note in a related technical report. "However, this particular sample doesn't need such a connection to begin the process. This eliminates the possibility of intercepting the keys exchange between the infected machine and the C&C server."
Unfortunately for victims, the strength of the encryption key used in the attack means it's not feasible to attempt to decrypt the files without having the remote private RSA key in hand. "The necessary time frame would be approximately two years and would involve using many computers," Check Point says.
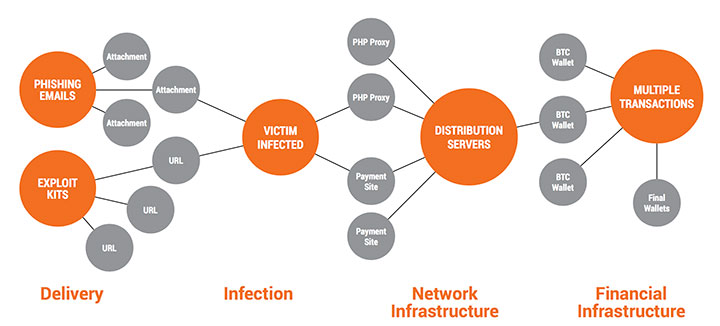
CryptoWall Ransom Demand Doubles
Arguably the most notorious malware now seen in the wild is CryptoWall. Since appearing in June 2014, it has netted criminals an estimated $325 million, the Cyber Threat Alliance reports in a 59-page technical teardown of Cryptowall version 3. The researchers behind the study - who hail from Barracuda Networks, Fortinet, Intel Security, Palo Alto Networks, ReversingLabs, Symantec, Telefónica, and Zscaler - add that to date, they have spotted 800 CryptoWall command and control URLs and over 400,000 infection attempts.
In June, the U.S. Internet Crime Complaint Center - a collaboration between the FBI and National White Collar Crime Center - reported receiving nearly 1,000 CryptoWall-related complaints since April 2014, and said related fees included "network mitigation, network countermeasures, loss of productivity, legal fees, IT services and/or the purchase of credit monitoring services for employees or customers."
Buoyed by their success to date, the CryptoWall gang has just released version 4 of their malware and bumped up their ransom demands, warns security firm Webroot. The major new features of the upgrade include improved C&C communications, plus scrambled filenames, so victims won't even know which encrypted files are which, says malware expert Lawrence Abrams in a blog post.
"These changes not only make it more difficult for the victim to identify what files have been encrypted, but also may thwart security protections currently in place for the CryptoWall threat," researchers at security firm Palo Alto Networks say in a Nov. 5 blog post.
Victims whose PCs have been infected with CryptoWall - and their files encrypted - see a ransom-demand page that helpfully informs them: "Congratulations! You have become a part of large community CryptoWall," adding that their files have been encrypted using 2,048-bit RSA key, says Webroot threat analyst Tyler Moffitt in a Nov. 5 blog post. If victims visit the website attackers have set up to receive ransom payments - supposedly in exchange for a decryption key - "we can see they immediately want $700," he adds. "It wasn't even a year ago when the default payment was $300." The ransom-payment page further warns that unless victims pay up within one week, the ransom demand will double to $1,400.
Anatomy of a CryptoWall Attack
Chimera Threatens to Leak Data
The gang behind yet another type of ransomware known as Chimera, which was first spotted in October, has been targeting victims via emails that offer fake job applications and business offers, warns the Anti-Botnet Advisory Center, which is a service of Germany's Association of the Internet Industry.
To date, these emails have included a link to Dropbox, requesting that the recipient download required files from an account at that file-sharing service, it says. In reality, however, the files are the Chimera ransomware. If executed, the file begins encrypting all local files, as well as files found in any network-attached storage devices. Once the computer reboots, users see a warning message demanding a one-time bitcoin payment of about 630 euros ($685) to decrypt the data. "To frighten the user even more, the message indicates the threat to publish personal data and pictures somewhere on the Internet - if user doesn't pay the bribe," the Anti-Botnet Advisory Center says.
Ransom Payments: No Guarantees
To date, it's not clear how many organizations have been infected with Chimera, or if attackers have been following through on their threat to spill stolen secrets online. Regardless, "never ever pay the cybercriminals if you have been infected by ransomware," the Anti-Botnet Advisory Center warns, echoing longstanding advice from security experts. Instead, it's urging businesses to maintain backups, so that if they fall victim to malware that encrypts any files, they can simply restore an unencrypted version of those files.
Indeed, paying a demanded ransom is no guarantee that attackers will share the decryption key or tools that are required to decrypt files. That's why security experts recommend putting the defenses in place to combat three increasingly common types of online extortion: ransomware, distributed denial-of-service attacks as well as the theft of sensitive business information.
With the quantity of online extortion attacks continuing to increase, the U.S. Federal Financial Institutions Examination Council this week issued an alert urging financial institutions to "develop programs to ensure the institutions are able to identify, protect, detect, respond to and recover from these types of attacks." And to defend against these types of extortion attempts, many security experts recommend that organizations employ DDoS-mitigation services and ensure that they have adequate backup and restoration capabilities via off-site storage.
ProtonMail Pays, Then Suffers
Of course some firms don't prepare, do pay the demanded ransom, and then still suffer. That appears to be what happened after Geneva-based encrypted email service ProtonMail on Nov. 3 paid $6,000 worth of bitcoins to attackers, after they disrupted the ProtonMail site for 15 minutes as a taster, then threatened to knock the service completely offline for an extended period of time. But after paying the ransom, ProtonMail says in a blog post that attackers unleashed the DDoS disruption anyway against its Internet Service Provider, which resulted in access for hundreds of other organizations being disrupted.
"We were placed under a lot of pressure by third parties to just pay the ransom, which we grudgingly agreed to do," it says. "We hoped that by paying, we could spare the other companies impacted by the attack against us, but the attacks continued nevertheless."
Security expert Graham Cluley says the episode demonstrates why victims should never accede to ransom demands.
@martijn_grooten Shut down. Change service provider. Get DDoS protection. Paying blackmailing DDoSers doesn't work
” Graham Cluley (@gcluley) November 5, 2015"Don't pay Internet blackmailers. All you have done is told the extortionists that you will consider giving them money for their crimes, and there is no guarantee that they - or other criminals - won't try it again and again and again," Cluley says in a blog post. "Paying blackmailers is only going to encourage more attacks, and is making the Internet a less safe place for all of us."