Fraud Management & Cybercrime , Next-Generation Technologies & Secure Development , Ransomware
Microsoft Issues Another Emergency Windows XP Patch
Mega-Worm Defense: Fresh Patches for Unsupported Operating Systems
Microsoft fears that nation-state actors may unleash viral code that could devastate users. On Tuesday, it released software fixes again for its older operating systems in hopes of averting a repeat of last month's infection of tens of thousands of computers with ransomware.
See Also: Break the Attack Chain with XDR
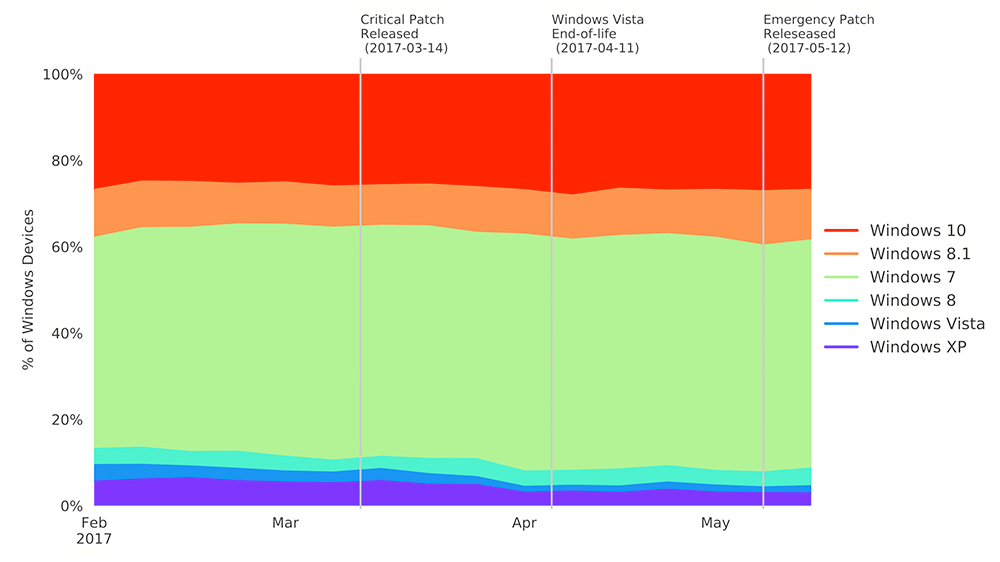
It's the second time in a month Microsoft has taken the unprecedented move to patch those systems, which include Windows XP, Server 2003, Vista and Windows 8. But the company sought to emphasize that updates for older systems will not be routine.
"Our decision today to release these security updates for platforms not in extended support should not be viewed as a departure from our standard servicing policies," writes Eric Doerr, general manager of Microsoft's Security Response Center, in a blog post.
Microsoft published a list of 15 vulnerabilities it believes are at "imminent risk" of being exploited, some of which date back to 2008 and 2009.
Cleaning House
Microsoft took an unprecedented step in May to patch older systems. Those updates blocked attacks using exploits likely stolen from the National Security Agency and released by a mysterious group called The Shadow Brokers (see WannaCry Outbreak: Microsoft Issues Emergency XP Patch).
This month's patches, released on Tuesday, clean up vulnerabilities that could be attacked with The Shadow Broker exploits as well as older issues, some going back as far as nine years, that could still pose a risk.
Microsoft is "sort of cleaning the house," says Amol Sarwate, director of engineering at Qualys.
The company does not want to see a repeat of WannaCry, the virulent ransomware that was engineered into a worm, the term for self-propagating code. The worm, which used an exploit from The Shadow Brokers dump, infected 200,000 computers worldwide (see WannaCry Ransomware Outbreak Spreads Worldwide).
Microsoft patched the vulnerability exploited by WannaCry in its newer operating systems a month before The Shadow Brokers released the exploit. But many computers were still vulnerable since the patch was not installed. Administrators often delay patching due to incompatibility with other applications.
Some vulnerabilities that Microsoft patched on Tuesday have the potential to be used for fast-spreading worms, says Dustin Childs, who works with Trend Micro's Zero Day Initiative project, which tracks software flaws. But it remains to be seen if organizations will patch.
"It's easy to say 'just apply the patch,' but the reality can be quite different," Childs says. "There are many reasons - some even valid - why patches aren't applied. Still, good patch hygiene remains the best method for preventing future malware outbreaks."
NSA Exploits
In its March patching round, Microsoft released fixes to defend against most of The Shadow Brokers' exploits. But it declined to issue patches for software vulnerabilities used by three exploits in The Shadow Brokers' cache: EnglishmanDentist, EsteemAudit and ExplodingCan.
On April 14, Microsoft said that those exploits didn't affect its supported platforms. Rather than issue fixes, the company encouraged those on older platforms to upgrade to newer versions of Windows.
But it appears over the last couple of months that the stakes are now higher and many users aren't going to upgrade. There's also a potential for a looming public relations disaster for Microsoft if another mass ransomware infection occurs.
In explaining its patches for older systems, Microsoft writes in a blog that the updates will "protect against potential nation-state activity." It did not specify what country may be involved, and a spokesperson did not provide additional information.
Adrienne Hall, general manager for Microsoft's Cyber Defense Operations Center, writes in a separate blog post: "Due to the elevated risk for destructive cyber attacks at this time, we made the decision to take this action because applying these updates provides further protection against potential attacks with characteristics similar to WannaCrypt."
Sarwate says Microsoft is in a delicate position. It doesn't want users to get infected on a mass scale. But it also doesn't want users on, say, XP to expect they will get patches for severe vulnerabilities, thus further delaying system upgrades.
"Personally, I think they did the right thing, but it's sort of a double-edged sword," Sarwate says. "You don't want people to get an impression that it's OK if I'm on an unsupported platform."
Use of unsupported Microsoft operating systems is widespread. A new report from security ratings service BitSight Technologies that examined over 35,000 organizations worldwide across 20 industries found that 24 percent of all systems are using an out-of-date internet browser. In addition, at 6 percent of organizations, more than half of their computers use outdated operating systems. The government sector in particular relied on outdated systems; more than 25 percent of all systems were outdated. Of those, nearly 80 percent were MacOS systems.
SMB, Again
Microsoft issued a total of 94 updates Tuesday. Of those, 27 flaws are remotely exploitable, the most dangerous kind of software flaw.
Microsoft fixed several flaws related to SMB, short for server message block, which is a network file-sharing protocol. WannaCry used a SMB flaw to quickly spread to other vulnerable computers on a network.
One of the SMB flaws patched by Microsoft on Tuesday, CVE-2017-8543, is being exploited in the wild. According to Microsoft's write-up, an attacker could send specially crafted SMB messages to the Windows Search service, allowing the remote takeover of a computer.
"That certainly reads like a wormable bug, albeit one that could possibly be contained within an enterprise," Childs writes in a blog post. "Either way, this is just the type of vulnerability favored by malware authors to create widespread chaos."
Executive Editor Mathew Schwartz also contributed to this piece.