Events , RSA Conference , RSA Conference Featured
Breaches: How to Protect Your Data
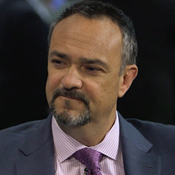
Trend Micro's Kellermann on Improving Threat Response
The threat landscape is constantly changing, and so is the information deemed valuable to hackers. While 2014 was the so-called year of the breach, when consumer card data was the hottest commodity, 2015 has been marked by more attacks aimed at compromising personally identifiable information and corporate intellectual property.
See Also: Using DPM and MITRE ATT&CK to Improve SOC Effectiveness
In an interview recorded at RSA Conference 2015, Tom Kellermann of Trend Micro discusses:
- How organizations can determine what data is most likely to be targeted;
- Why vendors are playing more active roles in helping their clients share intel with law enforcement;
- Why traditional methods of preventing data compromise are failing and what businesses should be doing better.
Kellermann, chief cybersecurity officer at Trend Micro, is a certified information security manager who analyzes emerging cybersecurity threats as well as relevant defensive technologies. Before joining Trend Micro, he served on The Commission on Cyber Security for the 44th Presidency. He also was vice president of security at Core Security for six years and previously worked as a senior data risk management specialist for the World Bank Treasury Security Team.
Additional Summit Insight:
Hear from more industry influencers, earn CPE credits, and network with leaders of technology at our global events. Learn more at our Fraud & Breach Prevention Events site.