3 Ways to Fight the Insider Threat
Tips to Help Prevent Malicious and Accidental Breaches
Increasingly, social engineers target insiders to plunder organizations' financial and intellectual assets. How can you prevent these and traditional inside attacks? Carnegie Mellon University's Dawn Cappelli offers tips.
See Also: The Biggest & Boldest Data Breaches & Insider Threats of 2023
Cappelli, co-author of the new book The CERT Guide to Insider Threats, has studied insider crimes for over a decade. She sees the definition of "insider threat" evolving.
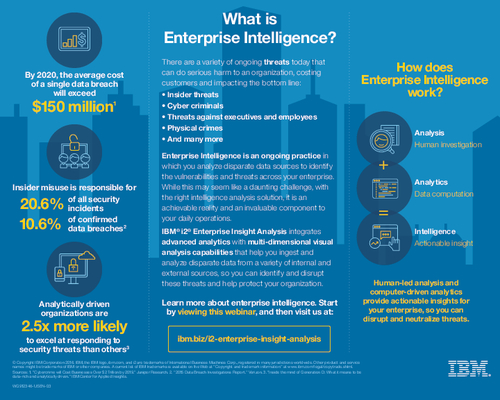
"We've been looking at malicious insiders," she says. "We define that as current or former employees, contractors, business partners - really, anyone who can get authorized access to your systems, your data, your network - and they intentionally misuse that access to do something bad.
But what about unintentional insider threats? "There are a lot of exploits that have happened this past year have been by external hackers that have used unintentional insiders to get into your network," she says. "We'd like to look at those [incidents] in the same way we've looked at malicious insiders all these years."
In an exclusive video interview recorded at RSA Conference 2012, Cappelli offers tips to combat insider crimes, including:
- The need for a formal insider threat program;
- How to leverage current technologies;
- How to identify and protect your "crown jewels."
Cappelli, CISSP, is Technical Manager of the Insider Threat Center and the Enterprise Threat and Vulnerability Management team in the CERT Program at Carnegie Mellon University's Software Engineering Institute. Her team's mission is to assist organizations in improving their security posture and incident response capability by researching technical threat areas; developing information security assessment methods and techniques; and providing information, solutions and training for preventing, detecting, and responding to illicit activity. Her team members are domain experts in insider threat and incident response, and team capabilities include threat analysis and modeling; development of security metrics and assessment methodologies; and creation and delivery of training, courses, and workshops. Cappelli has 30 years of experience in software engineering, including programming, technical project management, information security, and research. She is often an invited speaker at national and international venues, is an adjunct professor in Carnegie Mellon's Heinz College of Public Policy and Management and is currently Vice-Chair for the CERT Computer Security Incident Handler Certification Advisory Board.