Governance & Risk Management , Insider Threat
New Twist on Insider Crimes
What Happens When Your Trusted Business Partners Are the Threat?
This case exemplifies one of the more complicated questions about insider fraud: What happens when you're being pilfered by trusted third-parties?
Andrew Moore, a senior member of the CERT technical staff at the Software Engineering Institute (SEI), a unit of Carnegie Mellon University, says that of the 300-plus insider crime cases that CMU has studied, 45 of them are directly related to a trusted business partner. In these cases, "trusted business partner" is defined as any external business or individual that the institution has contracted with to do a service for the institution, which involves authorized access to organization data, networks and internal infrastructure.
Of these 45 cases, Moore says, two things standout: the types of insider crimes and the types of people who committed them. And the two factors are linked.
Crimes divide into two groups: those committed by people with an individual relationships with an organization, and those with an organizational relationship. Those insiders from organizational relationships committed more insider fraud and were after financial gain, Moore says. Sabotage was most often perpetrated by insiders who had individual relationships with an organization.
Organizational Relationships
Insiders with organizational relationships are typically in non-technical positions and have authorized access to those databases that they use to do their work. For these perpetrators, the crime is usually done at the business location -- most commonly fraud. Typically, there is more money associated with these relationships, Moore says, and so there is a greater motivation for fraud.
Individual Relationships
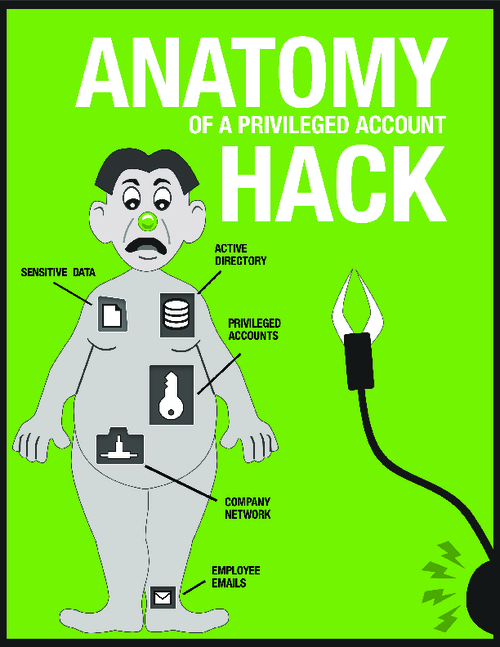
Insiders with individual relationships generally hold positions that are technical in nature, system administrators and the like. Their insider crimes utilize unauthorized access to the organization's systems.
"The typical consultant or contractor individual insider gets mad, they were released from their relationship with the institution, they were fired, or maybe their contract expired, and this upsets them," Moore says. The individual insider uses their technical knowledge to cause damage to the systems, either by planting a logic bomb or installing back doors before they were forced to leave, so they can come back afterward to perpetrate damage.
The individual insider typically attacks from a remote location, using the back doors they installed before leaving. "There are many different ways they can damage an organization, destroying data on databases -- they can do real harm to the organization," Moore says.
Another area of growing concern is the theft of intellectual property (IP). Where IP is concerned, client lists and databases are taken shortly before the insider leaves. IP data is usually taken within a month of the employee leaving, "So monitoring what they downloaded, emailed or printed out during their final days may uncover what they have taken with them," Moore says.
Other types of valuable IP for financial services firms could be proprietary software code used to run a trading platform, as well as trading algorithms. Anecdotally, Moore hears increasingly about financial services firms worried about insider theft of IP.
Cracking Down on Crime
How to prevent insider crimes by trusted business partners? Having clear contractual measures drawn up can help set new standards of doing business with the institution, including some of the security requirements. This is especially key when dealing with global partners.
"In many instances the overseas contractor and consultants aren't as security-conscious as an institution would like them to be," says security and privacy expert Larry Ponemon, founder of Ponemon Research. The stronger one can make the contractual agreement that holds the trusted business partner to strict security controls, the better the opportunity to keep possible insiders from doing harm.
Other tips include:
- Screen Employees -- "It doesn't have to be DOD level clearance, but a screening of personnel should be required," Moore says. In one case, CMU's research found where a person who had a criminal record was handling data as a trusted business partner's employee.
- Reinforce Policies -- Security procedures and policies should be at least at the same level of the institution, and all employees should be aware and comfortable using them.
- Monitor Exits -- Termination policies of the trusted business partners should be scrutinized and strengthened, if need. Moore says in many cases of sabotage, the insider was getting back into the organization's networks via backdoors installed on servers, causing damage, often without the business contractor knowing they had access. "If the trusted business partner isn't tracking access of its employees, it won't be able to disable it when the employee leaves the company," Moore notes. Reviewing logs upon an employee's departure may help spot where a back door was installed on a system, most of the sabotage events are done within a month of an employee's termination or resignation.
- Enforce Separation - insiders can't do fraud if someone else is doing part of the work. For critical transactions, a system of checks and balances should be a familiar process for institutions. People who are entering transactions shouldn't be able to approve them, too.
- Measure Access -- Be able to monitor the intellectual property to which employees and business partners have access. "Go with the least privilege access level, give only what they need in order to do their job," Moore says.